Xi Jinping’s High-Level Visit to Xiaomi Headquarters
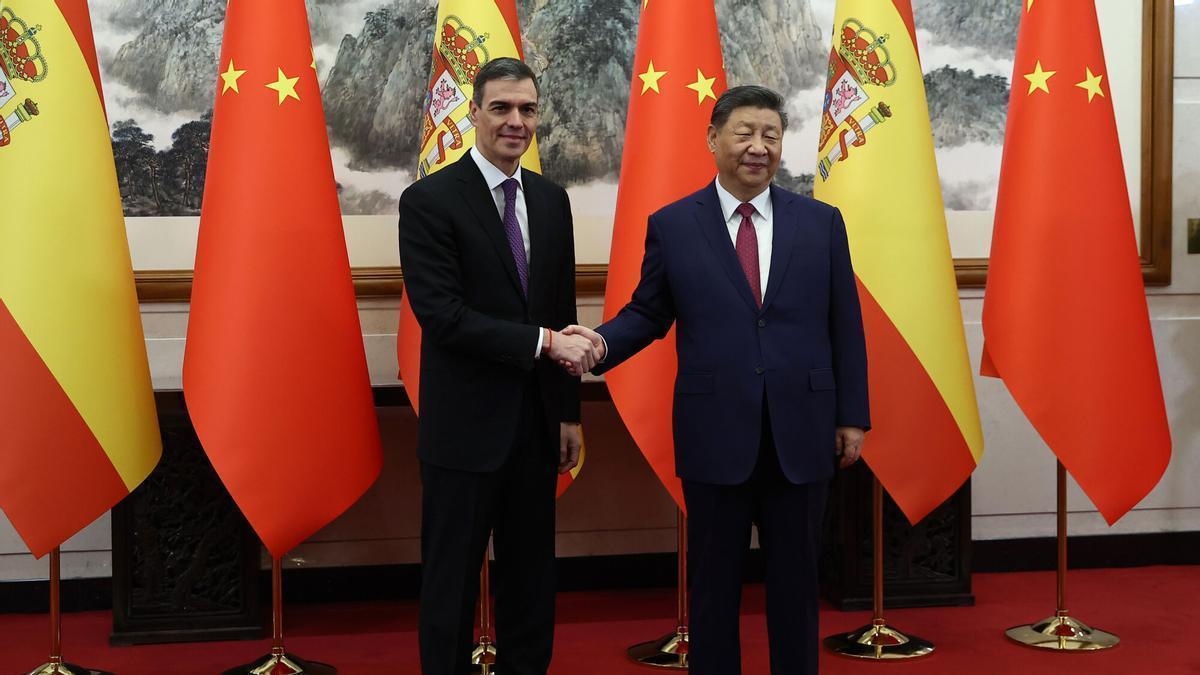
Spanish Prime Minister Sánchez is heading to Beijing to navigate the trade deficit and negotiate the terms of Chinese investments, a mission that includes a high-profile visit to Xiaomi’s headquarters. In a landscape where hardware is increasingly weaponized for diplomatic leverage, this visit occurs against a backdrop of heightened scrutiny over the intersection of consumer electronics and state security.
The Tech TL;DR:
- Hardware Diplomacy: Xiaomi devices are being used as state-level gifts to signal warming ties, notably between China and South Korea.
- Security Vectors: Explicit mentions of “backdoors” by Chinese leadership highlight the inherent risks in non-vetted hardware endpoints.
- Military Integration: Xiaomi’s involvement in machine learning studies with the People’s Liberation Army (PLA) and defense university funding raises red flags for Western joint ventures.
The optics of the Sánchez visit mirror a recent pattern of “hardware diplomacy” observed during the APEC summit in Gyeongju. Chinese President Xi Jinping gifted South Korean President Lee Jae Myung a pair of Xiaomi smartphones, a move that was as much a technological statement as a diplomatic one. The choice of Xiaomi—delivered to the home of Samsung Electronics—serves as a proxy for China’s broader economic development goals. Although, the exchange was marred by a pointed “joke” from Xi, who urged President Lee to “check if there’s a backdoor,” acknowledging the very vulnerability that keeps CISOs awake at night.
The Architecture of a ‘Backdoor’ and the Supply Chain Risk
From a technical standpoint, a backdoor is not a singular feature but a category of vulnerabilities. As defined in the context of the Xi-Lee exchange, it refers to a hidden method of bypassing normal authentication or security controls. For an enterprise, this represents the ultimate zero-day: a sanctioned entry point designed into the silicon or the firmware that bypasses the entire security stack. When hardware is gifted or integrated into state infrastructure, the blast radius of such a vulnerability extends from simple data exfiltration to full system compromise.

For organizations integrating third-party hardware into their ecosystem, the risk is not just in the software but in the SOC (System on a Chip) and the firmware. To detect unauthorized outbound connections—the “phone home” behavior typical of compromised devices—engineers often rely on packet inspection. If you suspect a device is communicating with an unauthorized C2 (Command and Control) server, a basic network audit is the first line of defense.
# Monitor outbound traffic from a specific device IP to identify unauthorized connections sudo tcpdump -i eth0 src [DEVICE_IP] and dst port 443 -vvWhile the “backdoor” comment was played off as humor, the underlying reality is documented in the relationship between Chinese tech giants and state security apparatuses. This isn’t theoretical vaporware; It’s a matter of architectural provenance. Companies that lack SOC 2 compliance or transparent audit trails for their firmware are increasingly viewed as liabilities in a zero-trust environment.
Military Links and the Machine Learning Pipeline
The risk profile of Xiaomi extends beyond consumer handsets into the realm of autonomous systems and AI. According to reports cited by the U.S. Select Committee on China, Xiaomi researchers have collaborated with the People’s Liberation Army (PLA) on machine learning studies. The company has provided funding for talent programs at China’s defense universities. This integration of commercial R&D with military objectives creates a blurred line between consumer tech and defense infrastructure.
This duality is currently creating friction in the automotive sector. Ford is reportedly pursuing a joint venture with Xiaomi, the maker of the SU7 sedan. This move has drawn sharp criticism from policymakers who argue that such partnerships deepen reliance on military-linked entities. Chairman John Moolenaar of the Select Committee on China highlighted the danger of this dependency:
“If it is true that Ford is starting a joint venture with Xiaomi it will be choosing to do business with yet another Chinese military-linked company. It will be turning its back on American and allied partners and it will make our country further dependent on China.”
For the CTO, the concern here is the “poisoning” of the supply chain. When a joint venture involves shared IP in machine learning and EV architecture, the risk of intellectual property theft or the insertion of dormant vulnerabilities increases. This is why enterprise IT departments are shifting toward rigorous cybersecurity auditors and penetration testers to validate every layer of their hardware stack before deployment.
The Geopolitical Tech Stack: Xiaomi vs. The West
The tension between Xiaomi’s market expansion and its state ties creates a complex matrix for global firms. On one hand, the hardware is competitive; on the other, the provenance is problematic. This is a classic conflict between performance and trust.
| Risk Factor | Consumer Impact | Enterprise/State Impact |
|---|---|---|
| Firmware Provenance | Minimal/Data Privacy | High (State Espionage/Backdoors) |
| ML Integration | Better UX/Features | High (Military Dual-Use Tech) |
| Supply Chain | Lower Cost | High (Geopolitical Dependency) |
As Sánchez seeks to condition Chinese investments, the focus will likely shift toward transparency and the decoupling of critical infrastructure from military-linked vendors. The “backdoor” joke may be a curiosity in a diplomatic banquet, but in a production environment, it is a critical vulnerability. Organizations cannot afford to rely on the goodwill of a vendor’s state; they must rely on verifiable code and hardware audits. To mitigate these risks, many firms are now employing Managed Service Providers (MSPs) to implement comprehensive supply chain risk management (SCRM) frameworks.
The trajectory of this technology suggests a future where “trusted hardware” becomes a premium tier of the market. We are moving toward a world where the origin of a chip is as critical as its clock speed. As we integrate more AI and ML into our physical infrastructure, the ability to audit the weights and biases of the underlying models—and the hardware they run on—will be the only way to ensure sovereign security.
Disclaimer: The technical analyses and security protocols detailed in this article are for informational purposes only. Always consult with certified IT and cybersecurity professionals before altering enterprise networks or handling sensitive data.
