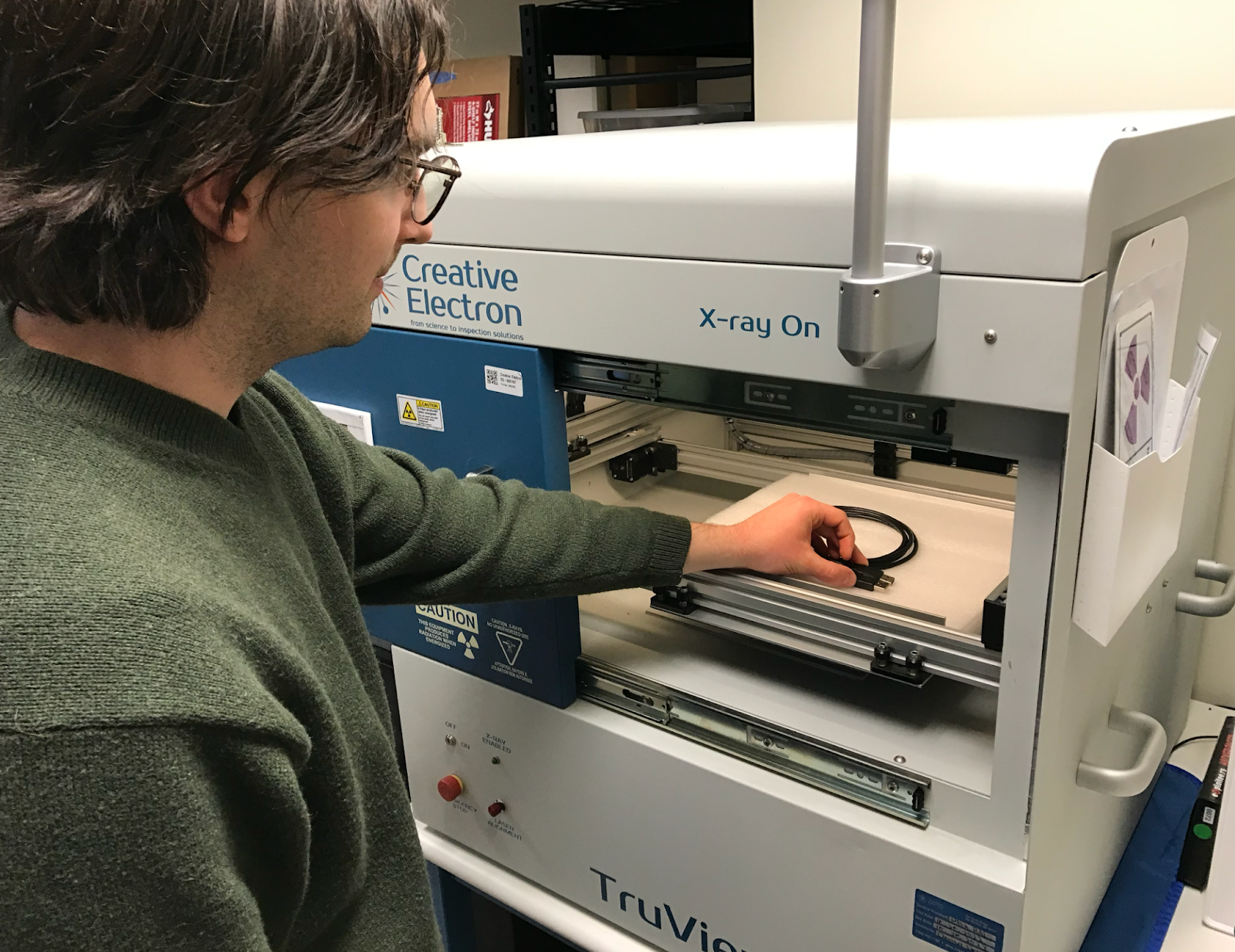
We recently acquired an industrial X-ray machine for the Eclypsium office to conduct serious cybersecurity research. Between X-raying unreleased industrial IT technologies for major companies—whose names we cannot disclose—we’ve undertaken some captivating experiments.
One experiment involved X-raying FTDI USB to UART cables. We had an older cable that appeared suspicious and performed poorly. It functioned at slow speeds but failed during firmware transfers.This prompted us to purchase verified cables from DigiKey, which worked as was to be expected. The older cable may have originated from a factory that also produced legitimate FTDI cables, but the chip didn’t meet FTDI’s performance standards. Alternatively, it might very well be a product of stolen FTDI intellectual property, or even an unrelated chip programmed to mimic FTDI in software. Without a precise silicon match to a known supply chain, speculation is all we can offer.
We wanted to compare the suspicious cable to a newer, demonstrably legitimate cable purchased from DigiKey for approximately $20. It’s reasonable to suspect a questionable-looking cable is counterfeit. FTDI has publicly reported issues with counterfeit devices, and has even deployed drivers that brick counterfeit chips—a practice some have labeled vendor-sanctioned malware.
Hear’s a visual comparison of the two cables:

And here are the X-rays:
The differences are striking. The legitimate cable shows clear,well-defined components and solder joints. The suspicious cable, tho, reveals a much messier internal structure, with poorly defined components and what appears to be a significant amount of filler material. The chip itself looks different, and the bond wires are much more haphazardly arranged.
This X-ray analysis confirms our suspicions: the cable is almost certainly a counterfeit.While we can’t definitively determine the origin or the extent of the counterfeiting operation, the visual evidence is compelling. This serves as a reminder that even seemingly innocuous components can be targets for counterfeiting, and that careful sourcing and verification are crucial for maintaining supply chain security.

