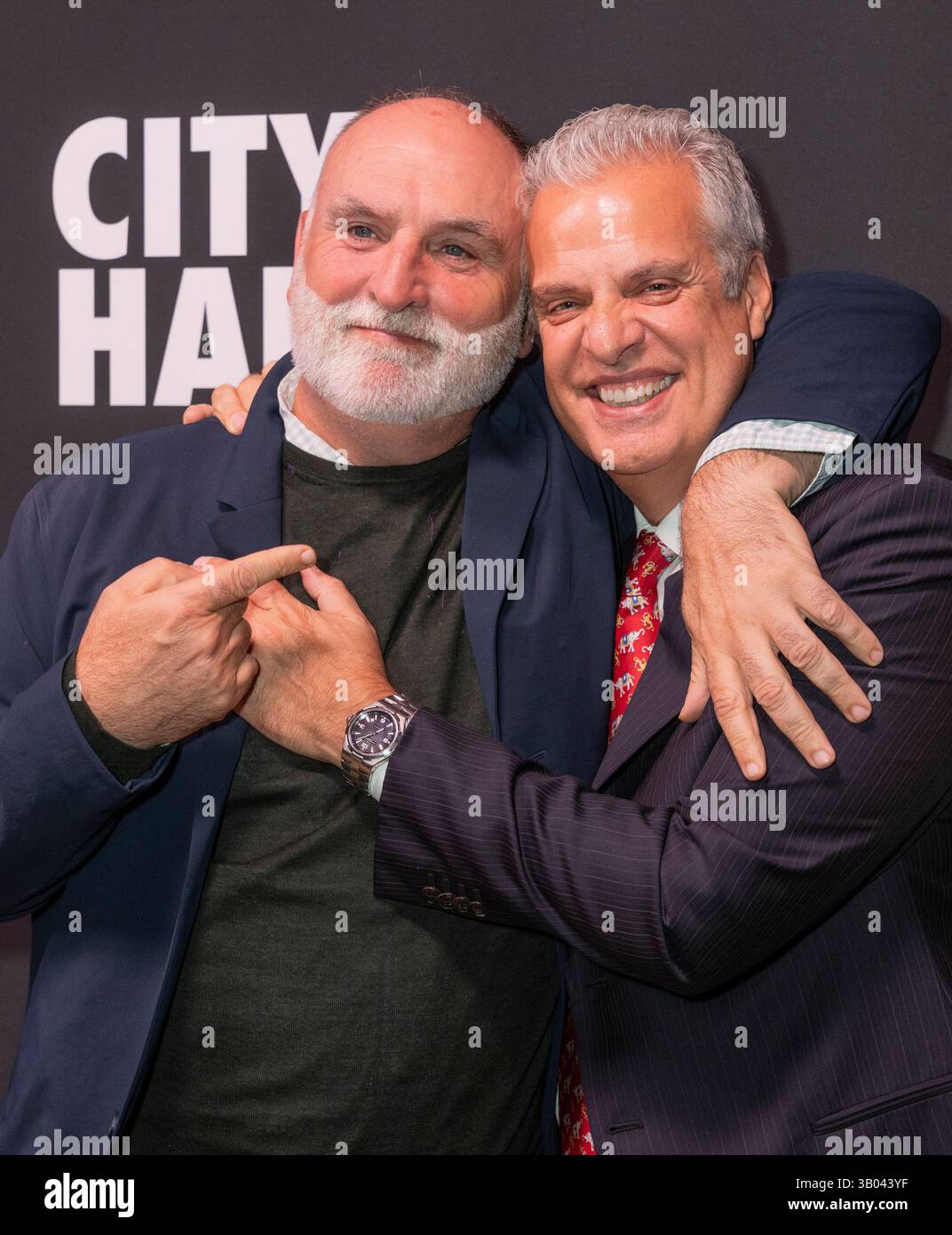
New Episodes Featuring José Andrés, Eric Ripert, Bill Ready and Iqram Magdon-Ismail
CNN is attempting to pivot its business authority through a “digital-first” deployment of its new series, The 1 on 1. By pairing high-profile CEOs—ranging from Pinterest’s Bill Ready to OpenAI Chairman Bret Taylor—in peer-to-peer interviews, the network is treating content as a lead-generation tool for its subscription streaming platform.
The Tech TL;DR:
- Strategic Pivot: Transitioning to a digital-first distribution model to increase the value proposition of CNN’s subscription-based streaming product.
- High-Value Network: Leveraging a roster of tech and business leaders (Rivian, Pfizer, Accenture) to build authority in the B2B vertical.
- Hybrid Distribution: Simultaneous rollout on a proprietary subscription platform and YouTube to optimize for both MRR (Monthly Recurring Revenue) and top-of-funnel reach.
The deployment of The 1 on 1 isn’t just a programming choice; it is a tactical move to solve a specific growth bottleneck. As Marie Beaudette, CNN’s VP of business and media, notes, the series is designed to “lift the curtain” on the strategy and decision-making of influential leaders. From an architectural perspective, this represents a shift toward “verticalization.” CNN is no longer just broadcasting news; it is building a business-centric vertical designed to attract a high-LTV (Lifetime Value) subscriber base that typically consumes content on platforms like LinkedIn or Bloomberg.
For a “digital-first” series to scale, the underlying infrastructure must handle volatile traffic spikes without introducing unacceptable latency. This requires a robust Content Delivery Network (CDN) strategy to ensure that high-bitrate video streams are cached at the edge, reducing the round-trip time (RTT) for global users. When legacy media houses transition to subscription models, they often encounter friction in the authentication layer. Implementing a seamless OAuth 2.0 flow is critical to prevent churn during the “paywall” transition. Companies struggling with this migration often engage cloud infrastructure consultants to optimize their API gateways and reduce time-to-first-frame (TTFF) metrics.
The Streaming Stack: Subscription vs. Open Access
The decision to launch on both a subscription platform and YouTube creates a complex distribution matrix. The subscription side focuses on exclusivity and data capture (SOC 2 compliance for payment processing), although the YouTube side focuses on algorithmic discovery. This dual-track approach allows CNN to A/B test content performance before locking the highest-value episodes behind a paywall.
| Metric | Subscription Platform (Proprietary) | YouTube (Open Access) |
|---|---|---|
| Monetization | Direct MRR / Subscription Fee | Ad-Revenue / Lead Gen |
| Data Ownership | First-party (Full User Profile) | Third-party (Aggregated Analytics) |
| Latency Target | Ultra-low (Edge Cached) | Standard (Google Global Cache) |
| Auth Layer | Strict (JWT / Session-based) | Permissive (Google Account) |
From a developer’s perspective, managing this hybrid rollout involves synchronizing metadata across different endpoints. To validate a user’s subscription status before granting access to an episode featuring leaders like Rivian CEO RJ Scaringe or Accenture CEO Julie Sweet, the backend typically executes a check against a subscription database. A standard implementation of this validation check might look like the following cURL request to a subscription API:
curl -X Gain "https://api.cnn.com/v1/subscription/validate?user_id=u98765&content_id=1on1_ep1" \ -H "Authorization: Bearer YOUR_ACCESS_TOKEN" \ -H "Content-Type: application/json"If the API returns a 403 Forbidden, the frontend triggers a redirect to the subscription landing page. This represents where the “friction” occurs. If the payment gateway has high latency or the UI is clunky, the conversion rate drops. This is why enterprise-grade media platforms prioritize Fetch API optimizations and asynchronous state management to keep the user experience fluid.
Alternative Content Distribution Frameworks
CNN’s approach competes directly with other B2B content strategies. While Bloomberg relies on a terminal-centric ecosystem and LinkedIn Learning focuses on skill acquisition, The 1 on 1 attempts to bridge the gap by focusing on “candid conversations” between peers. The “twist”—having the subjects interview each other—is essentially a social engineering play to bypass the standard PR-filtered responses typical of journalist-led interviews.

Though, the success of this model depends on the technical stability of the subscription vertical. Any outage during a high-profile drop (such as the episode featuring Pfizer CEO Albert Bourla) would result in significant brand erosion. To mitigate this, networks often employ cybersecurity auditors and penetration testers to ensure that the subscription endpoints are resilient against DDoS attacks and that user payment data is encrypted complete-to-end.
The current rollout, featuring figures like Venmo co-founder Iqram Magdon-Ismail and Pinterest CEO Bill Ready, serves as a stress test for this new business vertical. By focusing on “digital-first,” CNN is essentially treating its content as a software product—iterating on the delivery mechanism and the user acquisition funnel in real-time. For the CTOs and senior developers watching this, the real story isn’t the interviews themselves, but the attempt to migrate a legacy broadcast audience into a high-margin, subscription-based digital ecosystem.
As the series expands to include figures like Sierra Cofounder and OpenAI Chairman Bret Taylor, the pressure on the infrastructure will only increase. The trajectory is clear: legacy media is no longer just about the story; it is about the stack. The ability to scale a subscription product without compromising on latency or security is the only way to survive the shift from linear TV to digital-first authority.
Disclaimer: The technical analyses and security protocols detailed in this article are for informational purposes only. Always consult with certified IT and cybersecurity professionals before altering enterprise networks or handling sensitive data.
