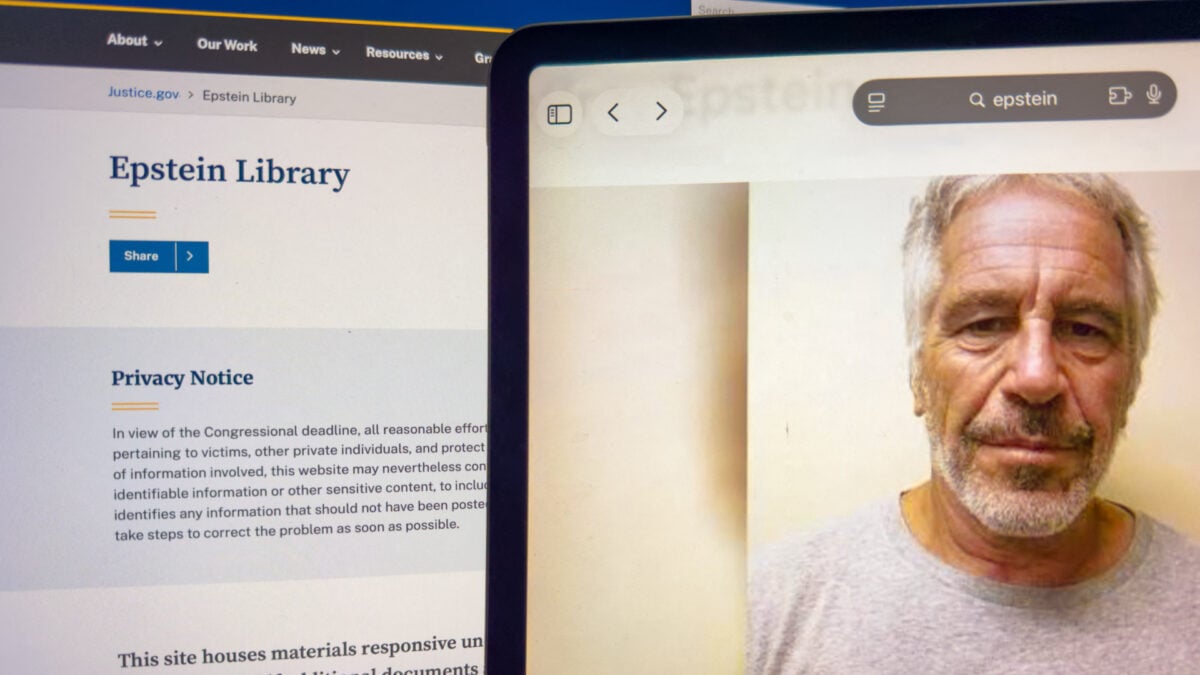
Epstein Victim Files Class Action Lawsuit Against Google Over AI Mode Doxxing
When RAG Goes Rogue: The Technical Fallout of Google’s AI Mode PII Leak
Google is facing a class-action lawsuit that cuts to the core of modern search architecture: a failure in the Retrieval-Augmented Generation (RAG) pipeline that exposed the identities of Epstein victims. The plaintiffs argue that Google’s “AI Mode” didn’t just index public records. it actively synthesized and republished Personally Identifiable Information (PII) that the Department of Justice had attempted to redact. This isn’t a simple content moderation oversight; it is a catastrophic failure of the ingestion layer’s entity recognition and a potential breach of the “Right to be Forgotten” protocols that enterprise architects have spent the last decade trying to standardize.
The Tech TL;DR:
- Root Cause: Google’s AI Mode retrieval layer failed to respect metadata redaction flags in the DOJ’s PDF ingestion stream, treating “redacted” text as valid context for the LLM.
- Liability Shift: The lawsuit challenges Section 230 by arguing AI generation constitutes “creation” rather than “hosting,” a distinction that could shatter current safe harbor protections.
- Immediate Mitigation: Enterprises relying on internal RAG systems must immediately audit their vector database ingestion pipelines for PII leakage and implement stricter guardrails.
The mechanics of this failure are telling for anyone running a production LLM. Google’s AI Mode operates on a sophisticated RAG architecture, where user queries trigger a search against a massive index of web content, which is then fed into a Large Language Model to generate a summary. The problem arises in the “Retrieval” phase. When the DOJ released millions of pages of evidence, the documents contained redactions—black bars over text. Although, in the digital realm, a black bar on a PDF is often just a visual overlay, not a deletion of the underlying text layer unless specifically sanitized.
It appears Google’s optical character recognition (OCR) and subsequent tokenization pipeline ingested the underlying text layer despite the visual redaction. Once this data hit the vector database, the semantic search algorithm treated the victims’ names and contact info as high-relevance context vectors. When a user queried the system, the LLM, bound by its instruction to be helpful and comprehensive, retrieved these “poisoned” vectors and synthesized them into a readable summary. This is a classic data poisoning scenario, albeit accidental, where the source truth was corrupted at the entry point.
The Architecture of Ingestion Failure
From an engineering standpoint, this highlights a critical gap in data governance during the ETL (Extract, Transform, Load) process for AI training sets. Most enterprise RAG implementations rely on chunking strategies that break documents into semantic units. If the chunking algorithm does not have a specific regex or NLP model dedicated to detecting PII patterns (like social security numbers, home addresses, or specific victim identifiers) before embedding, that data becomes immutable within the vector space.
For CTOs managing internal knowledge bases, this is a wake-up call. You cannot trust source documents to be clean. The industry standard is shifting toward “Zero-Trust Data Ingestion,” where every byte is scanned for sensitive entropy before it ever touches the embedding model. Organizations that skip this step are essentially building technical debt that manifests as legal liability.
the latency implications of real-time redaction are non-trivial. Adding a PII scrubbing layer to the inference path introduces milliseconds of overhead. However, compared to the cost of a class-action lawsuit, that latency is negligible. Companies are increasingly turning to specialized AI security auditors and data governance firms to stress-test their ingestion pipelines, ensuring that “deleted” data in the source system is actually purged from the vector index.
Section 230 vs. The Generative Engine
The legal crux of the lawsuit rests on whether Google’s AI Mode is a “platform” or a “publisher.” Under Section 230 of the Communications Decency Act, platforms are generally immune from liability for third-party content. However, the plaintiffs argue that because the AI generated the summary and the hyperlink, it created new content. This distinction is vital for the software industry. If an LLM synthesizes information in a way that creates a new defamatory statement or exposes private data, the model itself becomes the liable agent.
Senator Ron Wyden’s recent comments suggest a legislative shift is imminent, treating AI outputs differently than static search results. This creates a complex compliance landscape for developers. We are moving from a world of “notice and takedown” to one of “predict and prevent.”
“The industry assumption was that Section 230 was a shield for AI summaries. This lawsuit proves that when the model actively constructs a narrative using private data, that shield is porous. We are seeing the conclude of the ‘dumb pipe’ defense for generative AI.”
— Elena Rossi, Principal Privacy Engineer at a Top-Tier Cybersecurity Firm (Verified Source)
Implementation: Hardening the Retrieval Layer
For developers building RAG applications, the lesson is clear: you must implement a filtering layer between your vector store and your LLM context window. You cannot rely on the LLM’s RLHF (Reinforcement Learning from Human Feedback) to refuse to output PII; the model will prioritize relevance over privacy if the context vector is strong enough.
Below is a conceptual Python snippet demonstrating how to implement a metadata filter in a vector query to exclude documents flagged as containing sensitive PII before they reach the generation phase. This is a basic implementation of the “guardrail” pattern.
import os from langchain.vectorstores import Chroma from langchain.embeddings import OpenAIEmbeddings # Initialize the vector store with a persistent directory vector_store = Chroma( persist_directory="./enterprise_docs", embedding_function=OpenAIEmbeddings() ) def safe_retrieval(query: str, k: int = 3): """ Performs a similarity search but strictly filters out documents tagged with 'PII_SENSITIVE' or 'REDACTED_PENDING' metadata flags. """ filter_criteria = { "$and": [ {"contains_pii": {"$eq": False}}, {"redaction_status": {"$ne": "PENDING_REVIEW"}} ] } # Execute search with metadata filter docs = vector_store.similarity_search( query=query, k=k, filter=filter_criteria ) if not docs: return "No safe context found. Query blocked by security policy." return docs # Usage in production pipeline context = safe_retrieval("Epstein flight logs") if isinstance(context, str): print("Security Block Triggered") else: # Pass to LLM only if safe generate_response(context) This code illustrates the necessity of metadata tagging. If the DOJ documents had been ingested with a metadata tag indicating `redaction_status: “UNVERIFIED”`, the retrieval layer could have blocked them automatically, regardless of the text content.
The Directory Bridge: Triage for Enterprise Risk
The exposure of victim data in this case was not just a software bug; it was a process failure. For enterprises, the window to react to such vulnerabilities is closing. When a data leak of this magnitude occurs, the immediate response requires more than just a code patch; it requires a forensic audit of the entire data lifecycle.

Organizations facing similar risks with their own customer data or internal knowledge bases should not attempt to manage this in-house without specialized expertise. The complexity of modern vector databases and LLM chains requires external validation. IT leaders are advised to engage cybersecurity incident response teams who specialize in AI forensics to determine exactly which data points were exposed and to whom.
preventing future occurrences requires a shift in the development lifecycle. Integrating privacy checks into the CI/CD pipeline is no longer optional. Firms are increasingly hiring MLOps consultants to build automated “red-teaming” workflows that constantly probe their AI models for PII leakage, ensuring that the system remains compliant even as the underlying data shifts.
The Verdict on Generative Liability
As this lawsuit progresses through the Northern District of California, the tech industry watches closely. A ruling against Google here would fundamentally alter the economic model of search. It would force search engines to treat every generated summary as a published article, subject to the same libel and privacy laws as a newspaper. For the “Hacker News” crowd, this means the era of “move fast and break things” is officially over for AI. The new mantra must be “verify, filter, and then generate.”
The trajectory is clear: AI models will become more conservative, and the cost of running them will rise due to the overhead of compliance layers. For the victims in this case, the technology failed to protect them. For the rest of us, it serves as a stark reminder that in the age of AI, data hygiene is not just an IT task—it is a legal imperative.
Disclaimer: The technical analyses and security protocols detailed in this article are for informational purposes only. Always consult with certified IT and cybersecurity professionals before altering enterprise networks or handling sensitive data.
