Apple Leans Into Little Finder Guy With New TikTok Videos
Apple’s TikTok Gambit: UX Psychology vs. Enterprise Reality
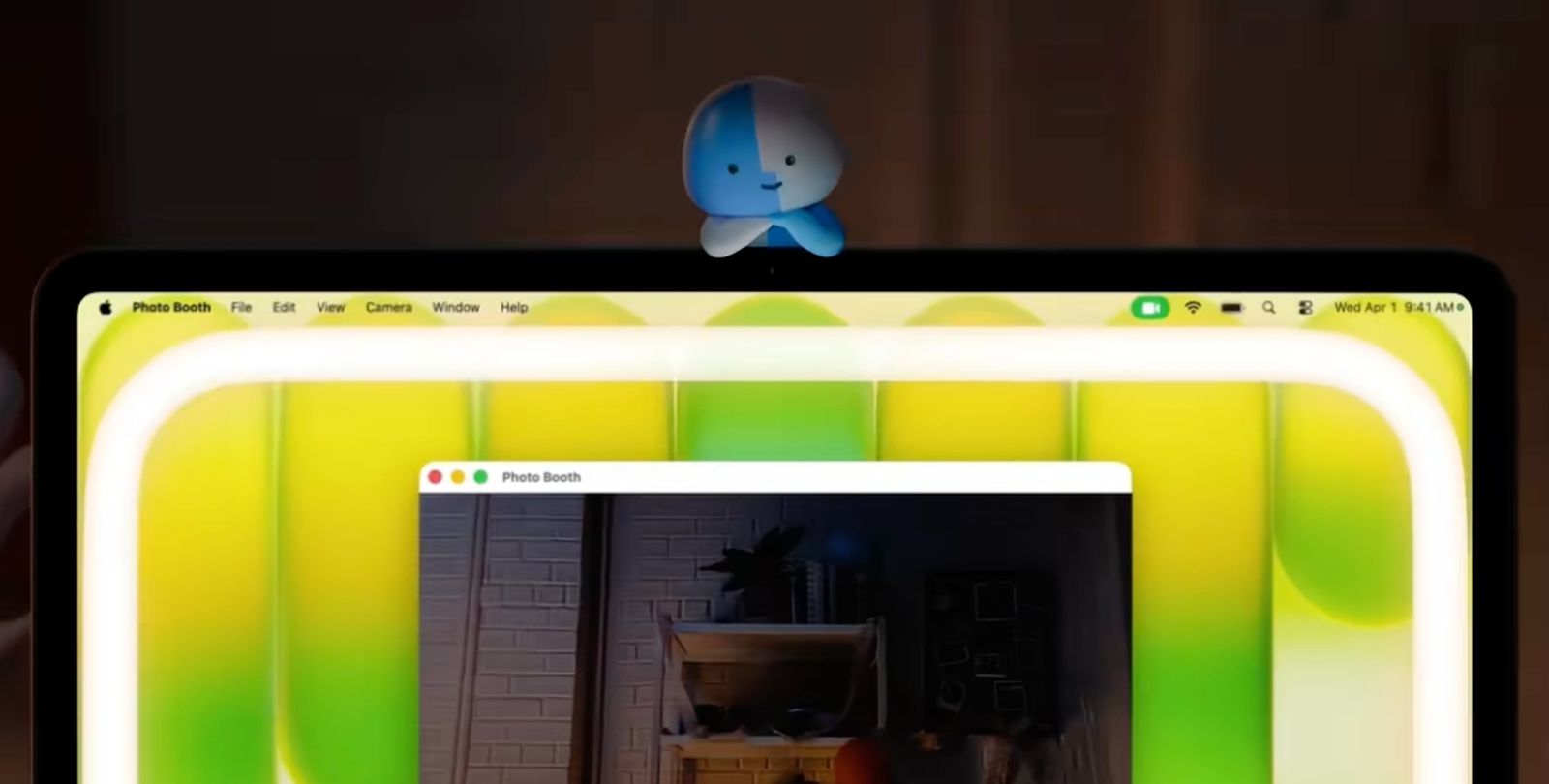
Apple is deploying a new vector for user acquisition, and it isn’t through the App Store search results. It’s through a series of intentionally bizarre TikTok vignettes featuring the “Little Finder Guy,” a CGI mascot designed to humanize the newly announced MacBook Neo. While marketing teams celebrate the engagement metrics, senior engineers and CTOs should be looking past the “Blush” and “Citrus” colorways to the underlying infrastructure shifts. This isn’t just a ad campaign; it’s a stress test of Apple’s ability to merge consumer virality with the rigid compliance requirements of their incoming Apple Business platform.
- The Tech TL;DR:
- Apple is utilizing high-velocity social algorithms to beta-test UI concepts for the upcoming Apple Business app launch on April 14.
- The “Little Finder Guy” campaign masks a deeper push toward integrated hardware-software ecosystems that bypass traditional MDM (Mobile Device Management) friction.
- Enterprises adopting the new MacBook Neo must immediately audit their endpoint security posture, as consumer-grade onboarding flows often introduce shadow IT vulnerabilities.
The “Little Finder Guy” videos, released in sets of three to correspond with the MacBook Neo’s color options, represent a departure from Apple’s usual polished, sterile aesthetic. This is deliberate. By injecting chaos and “meme-ability” into the launch cycle, Apple is gathering real-time sentiment data that traditional focus groups cannot provide. However, for the infrastructure architect, this signals a shift in how device provisioning will be handled. The MacBook Neo, with its rumored M5 architecture, is being positioned not just as a creative tool, but as a potential enterprise endpoint that relies on user familiarity rather than IT enforcement.
The Security Implications of Consumer-Grade Onboarding
While the marketing team focuses on Gen Z attention spans, the IT department faces a different reality. The source material indicates Apple is preparing to launch an Apple Business app alongside these hardware updates. This application promises to let employees install work apps and view colleague contacts with the same ease as a consumer TikTok scroll. This frictionless experience is the dream of UX designers but the nightmare of security auditors.

When onboarding becomes this seamless, the boundary between personal and corporate data blurs. We are seeing a trend where hardware vendors prioritize “delight” over “governance.” In a recent job posting for an Associate Director of Research Security at Georgia Tech, the emphasis was heavily placed on managing classified information within open research environments. This mirrors the challenge enterprises will face with the MacBook Neo: how to maintain SOC 2 compliance when the device itself encourages a consumer-like interaction model.
“The shift toward ‘invisible security’ in consumer hardware often means the user doesn’t understand they are secure until the policy enforcement fails. We require to move from reactive patching to proactive architecture.”
To validate the engagement velocity of this campaign against traditional developer interest, one might look at API traffic patterns. Below is a conceptual Python snippet demonstrating how a security team could monitor the correlation between viral marketing spikes and unauthorized API calls to corporate endpoints—a common side effect of “hype-driven” device adoption.
import requests import time def monitor_hype_correlation(hashtag, corporate_endpoint): """ Correlates social media velocity with internal API anomaly detection. Useful for identifying 'shadow IT' spikes during product launches. """ session = requests.Session() headers = {'Authorization': 'Bearer YOUR_ANALYTICS_TOKEN'} # Fetch social velocity (Hypothetical TikTok API endpoint) social_data = session.acquire(f'https://api.tiktok.com/research/hashtag/{hashtag}', headers=headers) velocity = social_data.json().get('video_count_per_hour', 0) # Check internal auth logs for anomaly internal_logs = session.get(f'{corporate_endpoint}/auth/logs?window=1h') anomaly_score = internal_logs.json().get('failed_auth_rate', 0) if velocity > 10000 and anomaly_score > 0.05: print(f"ALERT: High social velocity ({velocity}) correlating with auth anomalies.") return True return False # Example usage during MacBook Neo launch # monitor_hype_correlation('LittleFinderGuy', 'https://internal-corp-api.secure') Comparative Analysis: Viral Marketing vs. Enterprise Deployment
The “Little Finder Guy” strategy relies on emotional connection, whereas enterprise deployment relies on deterministic outcomes. The table below contrasts the metrics that matter to the marketing team versus the metrics that retain the CISO awake at night.
| Metric Category | Consumer Marketing (TikTok) | Enterprise IT (MDM/Security) |
|---|---|---|
| Primary Goal | Virality & Brand Sentiment | Compliance & Data Integrity |
| Success Indicator | Shares, Likes, Watch Time | Uptime, Patch Latency, Zero Trust Adherence |
| Risk Vector | Brand Dilution | Data Exfiltration, Ransomware |
| Deployment Speed | Instant (Algorithmic) | Phased (Pilot -> Production) |
This dichotomy creates a significant gap. As Apple pushes the narrative that the MacBook Neo is “ready for anything,” including the creative chaos of TikTok, they are implicitly suggesting that the device’s security model is robust enough to handle unvetted environments. However, history suggests otherwise. The introduction of new communication vectors, like the rumored Siri chatbot functionality mentioned in recent reports, expands the attack surface.
Organizations cannot rely solely on vendor promises. The complexity of modern supply chains and the integration of AI-driven features require external validation. This is where the role of third-party verification becomes critical. Just as Microsoft AI is hiring a Director of Security to oversee their own AI initiatives, your organization needs to ensure that the tools you adopt have undergone rigorous third-party scrutiny. This often necessitates engaging specialized cybersecurity consulting firms that can perform independent code audits and penetration testing on new hardware before it enters the production environment.
The “IT Triage” for the MacBook Neo
For CTOs evaluating the MacBook Neo for deployment, the “Little Finder Guy” campaign should serve as a warning label, not a selling point. It indicates a prioritization of user experience over granular control. If your organization handles sensitive data, the “frictionless” nature of the new Apple Business app could be a liability.

Before rolling out these devices, IT leaders should conduct a comprehensive cybersecurity audit specifically focused on the new OS features. Does the “Play Full Song” integration with TikTok introduce new background process permissions? Does the color-matching UI logic require access to camera or microphone data that could be exploited? These are not hypothetical concerns; they are the reality of 2026’s hyper-connected ecosystem.
the reliance on AI for features like the new Siri chatbot means that data processing may occur off-device. Understanding the data sovereignty implications is paramount. A risk assessment should be the first step in any procurement strategy involving these new Apple products. Do not let the charm of a CGI mascot obscure the architectural realities of the device.
Editorial Kicker
Apple’s mastery of narrative is unmatched, but in the enterprise sector, narrative does not patch vulnerabilities. The “Little Finder Guy” might win on the For You page, but in the server room, we deal in zeros and ones, not likes, and shares. As the MacBook Neo rolls out, the true test won’t be its thermal performance or its color accuracy, but whether its security model can withstand the pressure of a workforce that expects consumer-grade simplicity with enterprise-grade protection. Until then, keep your firewalls tight and your vendors accountable.
Disclaimer: The technical analyses and security protocols detailed in this article are for informational purposes only. Always consult with certified IT and cybersecurity professionals before altering enterprise networks or handling sensitive data.
