UTMStack: Simplifying Compliance in a Complex Regulatory Landscape
Organizations today face an increasingly complex web of regulatory requirements – from the Cybersecurity Maturity Model Certification (CMMC) and the Health Insurance Portability and Accountability Act (HIPAA) to the Payment Card Industry Data Security Standard (PCI DSS), SOC2, and the General Data Protection Regulation (GDPR). Achieving and maintaining compliance is challenging, frequently enough consuming significant time and resources that could be better allocated to strategic initiatives. Manual security control management is especially inefficient, prone to error, and struggles to keep pace with evolving threats and regulations.
Fortunately, solutions like UTMStack, an open-source Security Details and Event Management (SIEM) and Extended Detection and Response (XDR) platform, are emerging to streamline this process. UTMStack centralizes log data,correlates events,and automates compliance assessments,significantly reducing the burden on IT and security teams. This article delves into how UTMStack simplifies compliance management through automation, continuous monitoring, and reporting, offering a pathway to a more secure and efficient future.
understanding Compliance Automation with UTMStack
At its core, UTMStack thrives on data centralization. By collecting and correlating logs from disparate systems across the institution – servers, firewalls, applications, and more – UTMStack creates a unified view of the security landscape. This centralized view is the foundation for dynamic compliance assessments. Instead of relying on periodic, manual audits, UTMStack continuously processes real-time data to evaluate adherence to critical controls.
This extends to a broad range of essential security practices. UTMStack can automatically verify the use of encryption, confirm the implementation of multi-factor authentication (MFA), monitor user activity for suspicious behavior, and much more. This proactive approach not only ensures ongoing compliance but also drastically reduces the time and effort required to demonstrate it.
Figure 1: Automated evaluation of Compliance framework controls.
Example Compliance Control evaluations
Let’s examine how UTMStack evaluates specific compliance controls with concrete examples:
- Encryption Enforcement: Data encryption, both in transit and at rest, is a cornerstone of modern data security. UTMStack diligently monitors logs to identify instances where encryption is required. It checks for the presence and proper function of protocols like Transport Layer Security (TLS). For instance, an event indicating a failed TLS handshake due to an untrusted certificate—represented in logs as:
“message”: [{“The certificate received from the remote server was issued by an untrusted certificate authority. As of this, none of the data contained in the certificate can be validated. The TLS connection request has failed. The attached data contains the server certificate”.}]—immediately flags a potential compliance violation and alerts administrators. - Two-Factor Authentication (2FA): With the rise of credential-based attacks, 2FA is essential. UTMStack aggregates authentication logs to determine whether 2FA policies are consistently enforced across the organization. A prosperous 2FA authentication in Office365, such as, might appear in logs as:
’’authenticationDetails": [
{"authenticationStepDateTime": "2025-04-29T08:15:45Z","authenticationMethod": "Microsoft Authenticator","authenticationMethodDetail": "Push Notification", "succeeded": true,"authenticationStepResultDetail": "MFA requirement satisfied"}’’. Any deviations from the established 2FA policy trigger an immediate alert. - User Activity Auditing: Continuous monitoring of user and device activity is vital for detecting insider threats and unauthorized access. UTMStack provides comprehensive activity logs, scrutinizing privileged account usage, data access patterns, and identifying anomalous behavior that might indicate a compromise. This audit trail is automatically generated and assessed against defined compliance rules, eliminating manual review.
No-Code Compliance Automation Builder: Empowering Compliance Teams
One of UTMStack’s most powerful features is its intuitive, no-code compliance automation builder. Traditionally, building custom compliance frameworks required significant programming expertise. UTMStack eliminates that barrier, empowering compliance teams to create tailored assessments and automated workflows without writing a single line of code.
This is achieved through a drag-and-drop interface that allows users to visually define compliance control logic, establish real-time monitoring, and generate scheduled compliance reports. This versatility is invaluable for organizations needing to adapt to rapidly evolving regulations or those with unique compliance requirements.
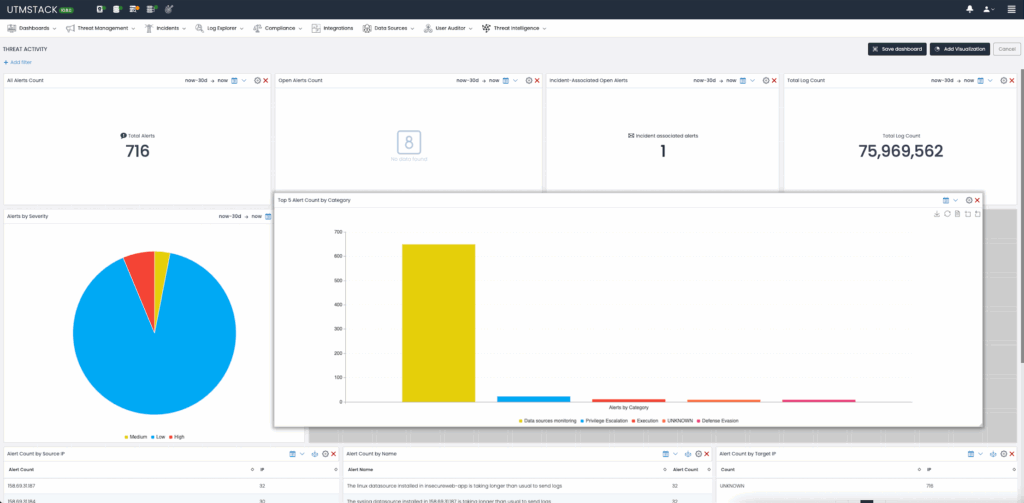
Figure 2: Compliance Framework Builder with drag and drop functionality.
Creating Custom Compliance Checks
With UTMStack’s no-code interface, teams can:
- Define custom compliance control logic visually, eliminating the need for coding expertise.
- Establish automated, real-time monitoring of specific compliance conditions, ensuring continuous oversight.
- Generate and schedule tailored compliance reports, providing stakeholders with timely and relevant information.
This streamlined approach minimizes administrative overhead and empowers compliance teams to respond rapidly to changing regulatory landscapes.
Unified Compliance Management and Seamless Integration
UTMStack isn’t just about automation; it’s about providing a centralized view of compliance efforts. The platform serves as a unified dashboard where controls fulfilled externally – through third-party assessments or documented processes – can be manually declared compliant. This ensures a holistic overview of compliance status, simplifying audits and reporting.
Moreover, UTMStack’s API-first architecture facilitates seamless integration with existing Governance, Risk, and Compliance (GRC) tools. This allows organizations to synchronize data,automate reporting,and centralize evidence,minimizing manual data handling and enhancing accuracy. Integration with established GRC platforms improves existing workflows, providing better openness and accountability.
Case Study: Streamlining CMMC Compliance
The Cybersecurity Maturity Model certification (CMMC) is a complex framework requiring organizations to demonstrate rigorous data security practices. UTMStack simplifies CMMC compliance by automatically evaluating controls related to data security, availability, processing integrity, confidentiality, and privacy. This is achieved by analyzing continuous log data – firewall configurations, user access patterns, audit trails, and more.
UTMStack’s automated reports clearly detail compliance status, including specific control numbers and levels, allowing organizations to proactively address issues and prepare for CMMC assessments and audits. This provides a significant advantage in navigating the complex requirements of the CMMC framework.
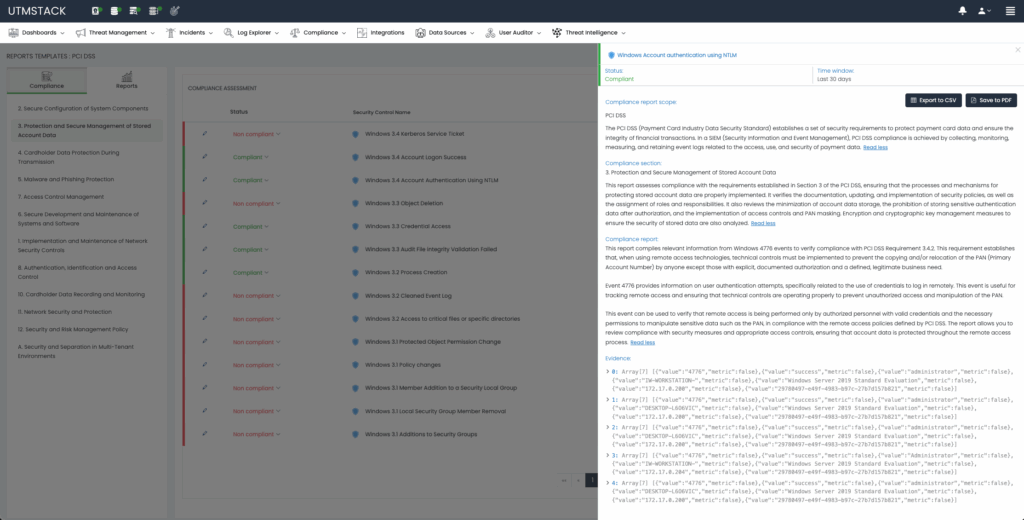
Figure 3: CMMC Compliance Control details
Automated Remediation with AI
when a compliance control fails, UTMStack goes beyond simply flagging the issue. Utilizing Retrieval-Augmented Generation (RAG), an AI-driven technique, the platform provides tailored remediation steps to security analysts and system engineers, accelerating the resolution process and reducing mean time to repair (MTTR).
UTMStack further enhances usability with intuitive dashboards that provide a comprehensive view of compliance status for each framework, enabling teams to quickly identify and prioritize areas needing attention.
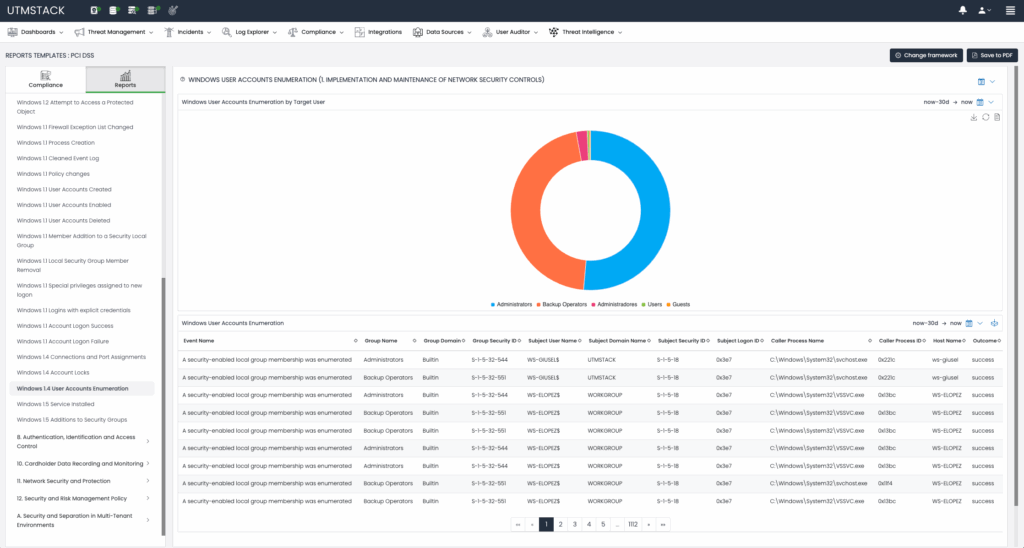
Figure 4: Compliance automation dashboards.
Conclusion: Embracing Automation for a More Secure Future
Compliance management no longer needs to be a resource-intensive and error-prone process. UTMStack’s open-source SIEM and XDR solution offers a powerful and accessible way to simplify and automate compliance with leading standards like CMMC, HIPAA, PCI DSS, SOC2, GDPR, and GLBA.By providing continuous monitoring, dynamic assessments, and a user-pleasant, no-code automation builder, UTMStack empowers organizations to reduce complexity, enhance efficiency, and focus on what matters most: innovation and growth.
As the regulatory landscape continues to evolve, embracing automation will be critical for organizations to remain compliant, secure, and competitive. UTMStack provides a vital tool for navigating this complex terrain and building a resilient cybersecurity posture.

