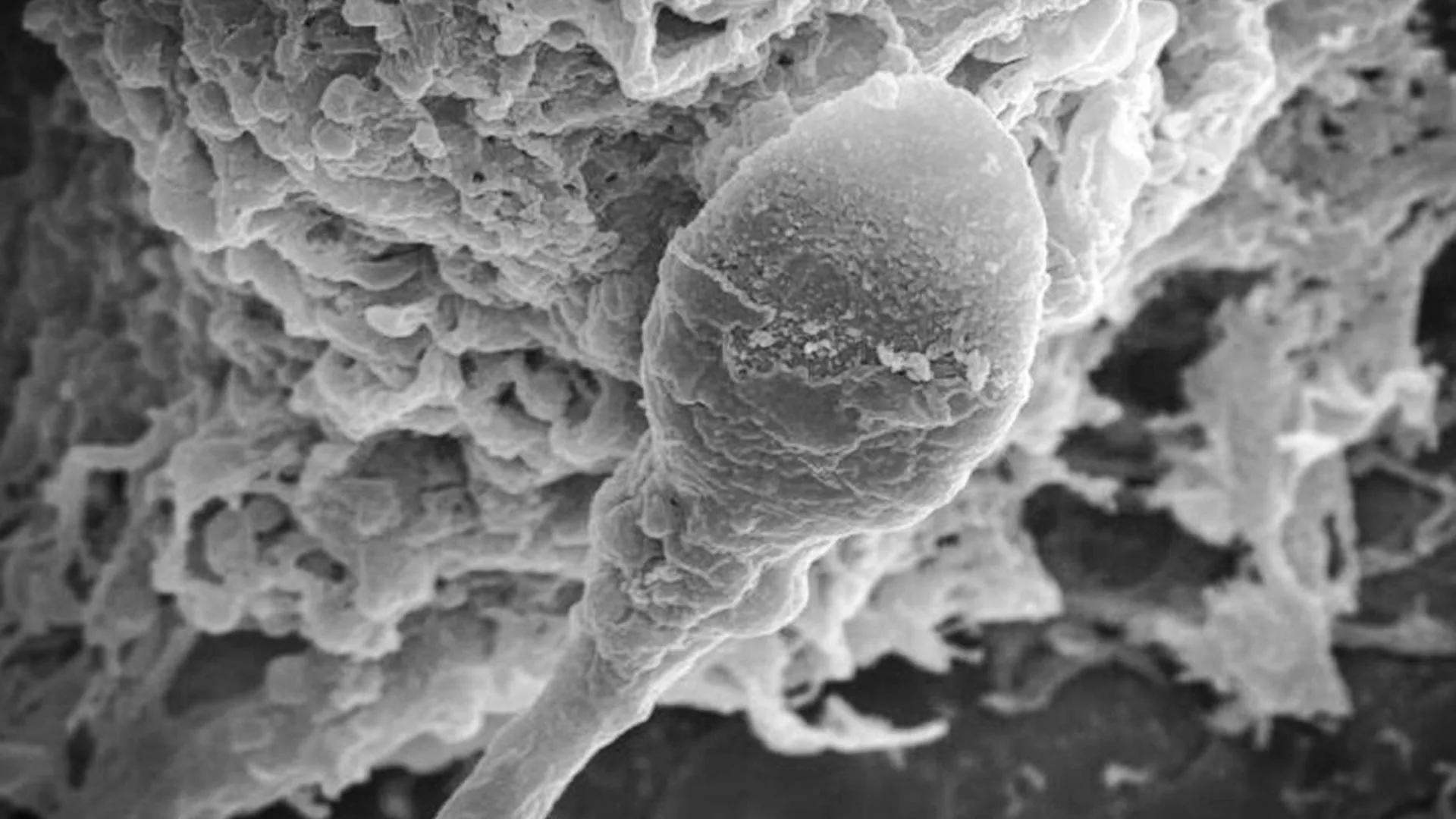
Space Reproduction: Low Gravity Impairs Sperm Navigation & Embryo Development
Microgravity Data Integrity: The Hidden Cybersecurity Risk in Space Reproduction Research
Adelaide University’s recent findings on sperm navigation in microgravity aren’t just a biological hurdle; they represent a critical data integrity challenge for long-term space mission architecture. When reproductive viability drops by 30 percent under simulated zero gravity, the telemetry logging that captures this degradation becomes high-value intellectual property. Securing the pipeline from the 3D clinostat to the cloud requires enterprise-grade cybersecurity audit services typically reserved for financial transaction networks.
The Tech TL;DR:
- Simulation Fidelity: 3D clinostat rotation introduces mechanical latency that must be accounted for in data timestamps.
- Data Sensitivity: Biometric reproduction data requires SOC 2 compliance equivalent to payment processing security.
- Infrastructure Gap: Current space-bound IT stacks lack dedicated AI security architects to protect model weights governing embryo development predictions.
The study utilized a 3D clinostat machine developed by Dr. Giles Kirby at Firefly Biotech to simulate microgravity. From an engineering perspective, this device is a rotational actuator system designed to vector-average gravity stimuli. Yet, the continuous rotation introduces potential signal noise in sensor readings. If the telemetry logging the sperm motility isn’t synchronized with the clinostat’s rotational phase, the dataset becomes corrupted. This isn’t merely a lab error; it’s a data integrity failure that could misguide multi-planetary settlement planning.
Researchers observed a significant reduction in navigation success without changes to physical motility. This suggests the guidance system—likely chemical gradients like progesterone—is disrupted by the lack of gravitational vectoring. For the software engineers modeling this behavior, the implication is clear: the AI models trained on Earth-based data will suffer from domain shift when deployed in low-earth orbit (LEO) or Mars transit. Retrainings cycles will spike, increasing the attack surface for model inversion attacks.
Hardware Specification and Security Overhead
Deploying biological experiments in space requires hardware that meets both scientific and security specifications. The clinostat must operate within strict thermal and power envelopes while maintaining encrypted data logs. We compared the typical lab setup against the requirements for space-hardened deployment.
| Component | Standard Lab Spec | Space Mission Requirement | Security Implication |
|---|---|---|---|
| Rotation Mechanism | DC Motor (Open Loop) | Stepper Motor (Closed Loop) | Prevents tampering with gravity simulation parameters |
| Data Logging | Local CSV Storage | End-to-End Encrypted Stream | Protects sensitive biometric IP during transmission |
| Power Supply | Mains AC | Redundant DC + Battery | Ensures integrity during solar flare events |
| Access Control | Physical Key | Multi-Factor Auth (MFA) | Aligns with cybersecurity audit standards |
The transition from local CSV storage to encrypted streams is non-negotiable. Biometric data regarding human reproduction is personally identifiable information (PII) with lifelong implications. A breach here isn’t just corporate espionage; it’s a violation of human rights protocols. Organizations like the AI Cyber Authority define this sector as one defined by rapid technical evolution and expanding federal regulation. Ignoring these standards invites liability.
As enterprise adoption of space-tech scales, the need for specialized oversight grows. The job market reflects this shift, with major entities like Visa and Microsoft posting roles for Sr. Director, AI Security. These positions aren’t just for fintech; they are blueprint roles for any industry handling sensitive algorithmic decisions. As noted in recent industry scope definitions, cybersecurity audit services constitute a formal segment of the professional assurance market, distinct from general IT consulting. You cannot patch biological data corruption with a software update.
“Cybersecurity consulting firms occupy a distinct segment of the professional services market, providing organizations with the assurance needed to validate complex bio-digital intersections.” — Security Services Authority Criteria
The research team examined how exposure to microgravity influences early embryo development, noting a 30 percent drop in fertilization rates after four hours. This data must be immutable. If a bad actor alters the timestamp or the gravity simulation logs, the scientific conclusion becomes invalid. Implementing a hash chain for every data point ensures that any tampering is immediately detectable.
Implementation Mandate: Data Integrity Hashing
To secure the telemetry from the clinostat, engineers should implement a SHA-256 hashing protocol for every data batch before transmission. This ensures that the data received on Earth matches the data generated in orbit. Below is a Python snippet demonstrating how to validate the integrity of a biological data log.
import hashlib import json def validate_bio_data_log(data_packet, expected_hash): """ Validates the integrity of biological telemetry data. Returns True if the data matches the expected SHA-256 hash. """ # Serialize data to ensure consistent hashing json_str = json.dumps(data_packet, sort_keys=True).encode('utf-8') # Generate hash calculated_hash = hashlib.sha256(json_str).hexdigest() if calculated_hash == expected_hash: return True else: raise ValueError("Data integrity check failed. Potential tampering detected.") # Example usage packet = {"motility": 0.45, "gravity_sim": "micro", "timestamp": 1711742580} # Hash would be generated at the source (clinostat) source_hash = "a1b2c3..." validate_bio_data_log(packet, source_hash) This level of rigor mirrors the standards expected by cybersecurity consulting firms when auditing high-stakes environments. The next phase of the Adelaide research involves exploring different gravity environments on the Moon and Mars. Each environment introduces new variables, effectively creating new edge cases for the data pipeline. Without robust continuous integration pipelines for the data itself, the scientific validity collapses.
Associate Professor John Culton of the Andy Thomas Centre for Space Resources emphasized the critical need for understanding these effects. However, understanding is useless without secure storage. As we progress toward becoming a spacefaring species, the IT infrastructure supporting reproduction research must be as resilient as the life support systems. This means engaging Managed Service Providers who specialize in high-latency, high-security environments.
The findings give hope that reproducing in space may be possible, but only if the data supporting that hope is trustworthy. The industry is moving toward a model where biological research is treated with the same security posture as financial transactions. The hiring of dedicated AI Security Directors at major corporations signals that the market recognizes this convergence. Ignoring the security layer of bio-simulation is a technical debt that future Mars colonies cannot afford to pay.
Disclaimer: The technical analyses and security protocols detailed in this article are for informational purposes only. Always consult with certified IT and cybersecurity professionals before altering enterprise networks or handling sensitive data.
