Rockwell Automation Stock Valuation Is ROK Overvalued At $351
Rockwell Automation (ROK): A Valuation Vulnerability or a Buying Opportunity in the OT Security Stack?
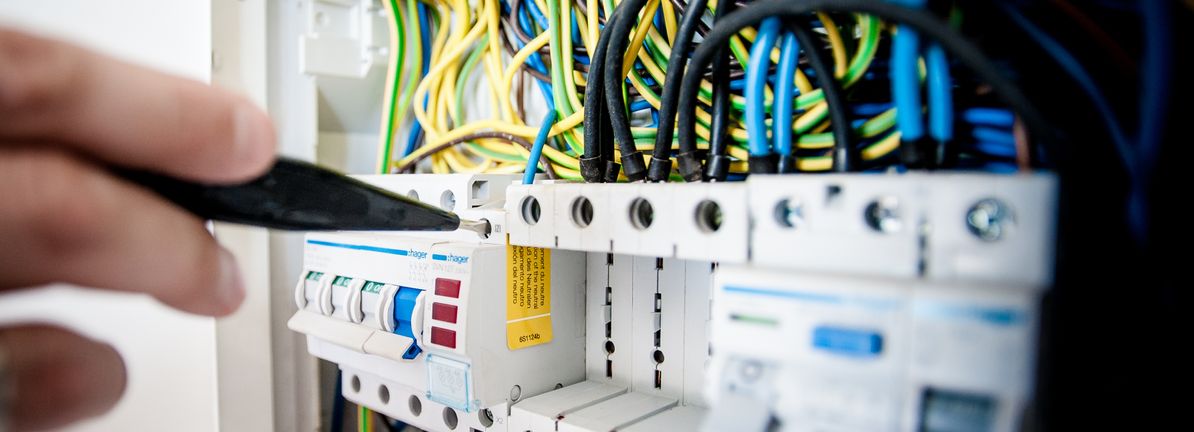
The market is pricing Rockwell Automation (ROK) at a 28.6% premium over its intrinsic DCF value, signaling a disconnect between Wall Street’s “Industry 4.0” hype cycle and the gritty reality of operational technology (OT) deployment. As a Principal Solutions Architect, I don’t look at P/E ratios in a vacuum; I look at technical debt. When a stock trades at 40x earnings while the underlying infrastructure faces escalating zero-day threats in industrial control systems, that premium isn’t growth—it’s risk exposure waiting to be realized.
The Tech TL;DR:
- Valuation vs. Reality: ROK is trading at a 40.0x P/E, significantly above the industry average of 31.6x, despite facing headwinds in supply chain localization and legacy protocol integration.
- Security Debt: The “Bear Case” highlights geopolitical and cyber risks; in technical terms, this translates to unpatched legacy PLCs exposed to modern AI-driven attack vectors.
- Directory Action: Enterprises relying on ROK ecosystems should immediately engage specialized OT cybersecurity auditors to validate network segmentation before scaling AI automation.
The DCF Disconnect: Pricing in Vaporware vs. Shipping Code
Simply Wall St’s Discounted Cash Flow model suggests an intrinsic value of $273.24 against a current price of ~$351.50. From an engineering standpoint, this 28.6% overvaluation implies the market is pricing in a “perfect deployment” scenario that rarely exists in brownfield industrial environments. The model assumes free cash flow will nearly double to $2.71b by 2035, driven by “AI-enabled automation.” However, anyone who has touched a legacy Allen-Bradley controller knows that integrating modern AI inference engines with 15-year-old ladder logic introduces massive latency and stability bottlenecks.
The “Bull Case” narrative assumes revenue growth of 7.18% annually, banking on factory digitalization. But digitalization isn’t just a software update; it’s a hardware overhaul. The latency introduced by wrapping legacy Modbus or EtherNet/IP traffic in modern TLS 1.3 tunnels for cloud analytics can cripple real-time control loops. If Rockwell cannot solve the edge-compute latency issue without sacrificing determinism, that projected $1.9b in earnings by 2029 is pure vaporware.
The Cybersecurity Blast Radius: Why the Bear Case Holds Water
The “Bear Case” valuation of $324.93 factors in geopolitical tension and supply chain disruption. Technically, this maps directly to the Supply Chain Cybersecurity risks highlighted in recent industry frameworks. As organizations depend more on third-party software components and hardware from vendors like Rockwell, the attack surface expands exponentially. We are seeing a shift where the value isn’t in the hardware, but in the secure management of that hardware.
Consider the hiring trends in the sector. Major tech players are aggressively recruiting for roles like Director of Security for AI and Sr. Director, AI Security. This talent war indicates that securing AI-driven industrial automation is the primary bottleneck, not the automation itself. If Rockwell’s software stack lacks the SOC 2 compliance and finish-to-end encryption standards that these new security roles demand, their premium valuation is unjustified.
“The convergence of IT and OT is where the security model breaks. We aren’t just patching servers anymore; we are patching physical machinery that can’t afford downtime. The market is undervaluing the cost of securing this transition.”
— Industry Consensus on OT/IT Convergence Risks (Synthesized from Security Services Authority Frameworks)
This is where the “IT Triage” becomes critical. If you are holding ROK or integrating their stack, you cannot rely on default configurations. You need to validate the security posture of your supply chain. This is the exact employ case for Supply Chain Cybersecurity Services that specialize in vendor risk assessment. The “Bear Case” isn’t just about earnings; it’s about the liability of an unsecured industrial IoT network.
Implementation Mandate: Auditing the Edge
Before buying into the “digitalization” narrative, architects need to verify the actual throughput and security of the edge nodes. Don’t trust the marketing slide deck; trust the packet capture. Below is a basic tcpdump command sequence to identify unencrypted industrial traffic on your local segment—a common vulnerability in legacy ROK deployments that drags down valuation by increasing risk profiles.
# Monitor EtherNet/IP traffic (Port 44818) for unencrypted payloads # Replace eth0 with your industrial network interface sudo tcpdump -i eth0 port 44818 -nn -v | grep -i "CIP" # Check for cleartext credentials or command injection attempts # This helps identify if legacy PLCs are exposed to modern MITM attacks sudo tshark -i eth0 -Y "enip.command == 0x04" -T fields -e ip.src -e ip.dstRunning this on a production floor often reveals that “digitalized” factories are still broadcasting control commands in cleartext. This technical reality supports the lower valuation multiple (26.6x P/E in the Bear Case) since the cost to remediate this technical debt—replacing hardware, implementing Cybersecurity Audit Services and re-architecting the network—will eat directly into those projected profit margins.
The Verdict: Hold for Security Patches, Not Growth
Rockwell Automation is a foundational piece of industrial infrastructure, but the current share price reflects a “greenfield” fantasy in a “brownfield” world. The 12.6% decline over the last 30 days is the market beginning to price in the friction of real-world deployment. Until we see concrete evidence of reduced latency in their AI edge stacks and a robust, audited security posture that matches the hiring trends of Microsoft and Visa, the stock remains technically overextended.
For the CTOs and investors reading this: The opportunity isn’t in the stock ticker; it’s in the remediation. The companies that will win in the next cycle aren’t just the hardware vendors, but the consulting firms that can secure the bridge between legacy automation and modern AI. If you must hold ROK, treat it as a utility play, not a growth hack, and budget heavily for the security overhead that the DCF model ignores.
Disclaimer: The technical analyses and security protocols detailed in this article are for informational purposes only. Always consult with certified IT and cybersecurity professionals before altering enterprise networks or handling sensitive data.
