Nuclear Propulsion: SR-1 Mission Aims for 2028 Mars Launch | Ars Technica
NASA’s SR-1 Freedom: Nuclear Propulsion Meets Supply Chain Reality
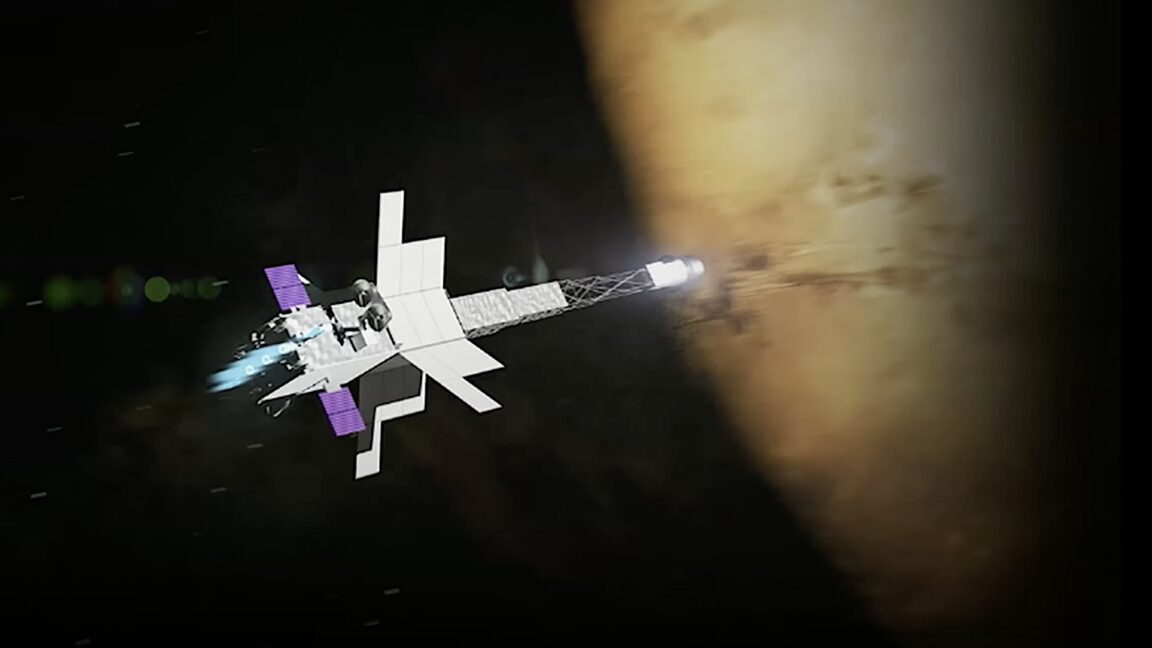
NASA is pivoting from greenfield development to hardware reuse for the SR-1 Freedom mission, aiming to slap a nuclear reactor onto an existing spacecraft bus for a 2028 Mars window. This isn’t innovation; it’s survival engineering driven by a $20 billion hole in previous program budgets. While the physics of nuclear-electric propulsion (NEP) offers superior specific impulse, the real bottleneck isn’t thrust—it’s the certification pipeline for launching radioactive material through Earth’s atmosphere.
The Tech TL;DR:
- Deployment Timeline: Mission design locks June 2026; assembly starts 2028 to hit the December 2028 Mars launch window.
- Security Surface: Nuclear payload certification requires DOE oversight and specialized launch vehicle hardening (e.g., Falcon Heavy nuclear cert).
- Operational Risk: Single-point failure on the reactor coupling; missed window delays mission to 2031 due to orbital mechanics.
The SR-1 program relies on a reactor that is “mostly built” and fuel “mostly paid for,” according to Jared Isaacman. This strategy reduces capital expenditure but increases integration risk. You cannot patch a nuclear core once it is sealed in the fairing. The architecture demands near-perfect execution on the ground as orbital mechanics does not negotiate. If the telemetry systems fail during the trans-Mars injection, there is no rollback mechanism. This shifts the critical path from propulsion engineering to systems assurance and compliance auditing.
Launching radioactive material triggers a complex web of federal regulatory requirements. The Department of Energy (DOE) must approve the safety analysis report (SAR) before any rocket leaves the pad. SpaceX’s Falcon Heavy is currently undergoing nuclear certification to support this payload class, mirroring the process used for the Dragonfly mission to Titan. This certification isn’t just about structural integrity; it involves rigorous cybersecurity validation of the launch vehicle’s avionics to prevent spoofing or unauthorized command injection during the ascent phase.
“Cybersecurity audit services constitute a formal segment of the professional assurance market, distinct from general IT consulting. For critical infrastructure like nuclear propulsion, the scope must include physical-digital intersection points.”
This distinction matters for the contractors building the ground control segments. As noted by the Security Services Authority, standard IT compliance frameworks often fail to capture the unique risks of operational technology (OT) in aerospace. The SR-1 mission requires providers who understand both nuclear safety protocols and digital threat vectors. Organizations managing similar high-stakes deployments are increasingly deploying vetted cybersecurity auditors and penetration testers to secure exposed endpoints before integration.
Propulsion Architecture and Risk Profile
The SR-1 Freedom mission utilizes conventional plasma thrusters energized by a nuclear reactor rather than solar arrays. This shift eliminates dependency on solar flux, which diminishes significantly beyond Mars orbit, but introduces thermal management challenges and radiation hardening requirements for nearby electronics. The table below breaks down the operational trade-offs between this NEP approach and traditional chemical propulsion.
| Metric | SR-1 Nuclear-Electric | Traditional Chemical |
|---|---|---|
| Specific Impulse (Isp) | 3,000 – 5,000 seconds | 450 seconds (LH2/LOX) |
| Thrust Level | Low (Continuous) | High (Impulsive) |
| Regulatory Overhead | Extreme (DOE/NRC) | Standard (FAA/AST) |
| Supply Chain Security | Critical (Nuclear Material) | Moderate |
The supply chain security for the nuclear component is the primary vulnerability. Any compromise in the manufacturing or transport of the fuel could ground the mission indefinitely. This requires a level of cybersecurity risk assessment and management services that goes beyond standard software bill of materials (SBOM) checks. It demands physical-digital twin verification.
Implementation: Telemetry Integrity Verification
For engineers integrating with the ground control systems, verifying the integrity of command packets is non-negotiable. Below is a simplified example of how a ground station might verify the hash of a critical propulsion command before execution, ensuring no man-in-the-middle alteration occurred during uplink.
#!/usr/bin/env python3 import hashlib import hmac def verify_command_integrity(command_payload, secret_key, received_hash): """ Verifies the HMAC-SHA256 hash of a propulsion command. Prevents unauthorized thrust vector adjustments. """ expected_hash = hmac.new( secret_key.encode('utf-8'), command_payload.encode('utf-8'), hashlib.sha256 ).hexdigest() if not hmac.compare_digest(expected_hash, received_hash): raise SecurityException("Command integrity check failed. Abort sequence.") return True # Example Usage cmd = "IGNITE_THRUSTER_CLUSTER_A" key = "SR1_SECURE_KEY_DO_NOT_DISTRIBUTE" hash_sig = "a1b2c3d4..." # Received from uplink try: verify_command_integrity(cmd, key, hash_sig) print("Command Authenticated. Executing.") except SecurityException as e: print(f"CRITICAL FAILURE: {e}") This level of cryptographic assurance is standard for modern space operations but must be audited rigorously. As the Security Services Authority outlines, consulting firms occupying this distinct segment of the professional services market provide the necessary oversight to ensure these protocols are not just implemented, but resilient against side-channel attacks.
Sinacore noted that the mission scope must bend around the 2028 deadline. There is no slack in the schedule for security incidents. A single ransomware event on the ground control network could miss the launch window, pushing the next opportunity to 2031. This latency risk forces enterprise IT departments supporting such missions to engage specialized practitioners operating at the intersection of artificial intelligence and cybersecurity to monitor network traffic for anomalies in real-time.
The SR-1 Freedom mission is a testament to engineering pragmatism, but it exposes the fragility of critical infrastructure when software timelines collide with nuclear regulatory realities. Success depends less on the thrust of the ion engines and more on the integrity of the supply chain and the security of the command uplink. As we move toward multi-planetary operations, the directory of trusted security providers becomes as vital as the launch manifest itself.
Disclaimer: The technical analyses and security protocols detailed in this article are for informational purposes only. Always consult with certified IT and cybersecurity professionals before altering enterprise networks or handling sensitive data.
