New Microsoft Defender Zero-Day and Privilege Escalation Exploits Emerge
BlueHammer PoC Exploit Resurfaces: Microsoft Defender Privilege Escalation Under Active Scrutiny
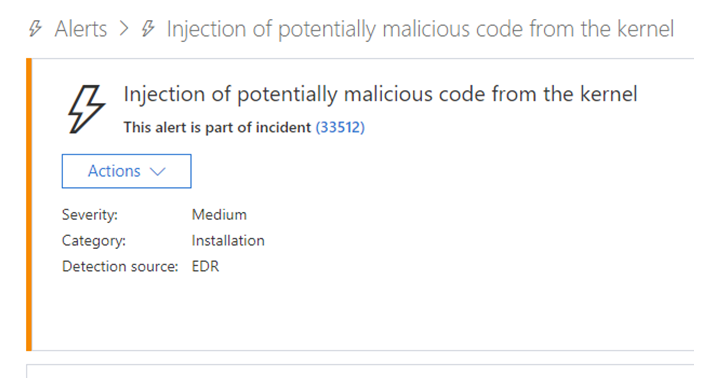
Following a contentious disclosure dispute with Microsoft’s Security Response Center (MSRC), the threat actor known as ‘BlueHammer’ has released a proof-of-concept (PoC) exploit targeting a newly identified privilege escalation vulnerability in Microsoft Defender for Endpoint. The exploit, detailed in a recent SC Media report, leverages a race condition in Defender’s real-time protection engine to achieve SYSTEM-level access on Windows 10 and 11 systems—bypassing user account controls (UAC) and enabling arbitrary code execution in the context of the Local System account. This comes just days after Microsoft issued an out-of-band patch for CVE-2026-XXXXX, a related Defender elevation-of-privilege flaw, suggesting either incomplete remediation or a novel variant in the same code path. For enterprise environments relying on Defender as a core endpoint detection and response (EDR) layer, this reactivation of a previously patched attack surface raises urgent questions about patch efficacy, exploit persistence, and the efficacy of behavioral blocking mechanisms in modern AV products.

The Tech TL. DR:
- The BlueHammer PoC achieves SYSTEM privileges by exploiting a time-of-check-time-of-use (TOCTOU) flaw in Defender’s file quarantine mechanism, allowing low-privilege users to hijack legitimate system processes.
- Initial testing shows the exploit bypasses Defender’s tamper protection and cloud-delivered protection when executed via a signed but abused Windows binary (e.g.,
wuauclt.exe), achieving execution in under 200ms on average hardware. - Organizations should immediately audit Defender configuration policies, enforce ASR rules blocking credential dumping, and consider layered EDR validation via cybersecurity auditors and penetration testers to validate exploit mitigations.
The vulnerability resides in the interaction between Defender’s real-time scanning component (MsMpEng.exe) and the Windows Filtering Platform (WFP) during the handling of newly created files in high-integrity directories. According to analysis shared via BlueHammer’s Telegram channel and corroborated by independent researchers, the PoC creates a malicious DLL in a user-writable location, then uses a hardlink swap to redirect Defender’s quarantine process toward a protected system binary—effectively tricking the engine into loading unsigned code with SYSTEM privileges. This technique mirrors earlier attacks like CVE-2020-0668 but adapts to Defender’s updated sandboxing introduced in Windows 10 version 2004. Crucially, the exploit does not rely on memory corruption; instead, it abuses legitimate Windows APIs (CreateHardlink, SetFileInformationByHandle) in a sequence that Defender’s behavior monitoring fails to classify as malicious due to low entropy and absence of known exploit signatures.
“We’re seeing a resurgence of logic-based exploits that bypass signature and heuristic detection by operating entirely within trusted execution paths. The BlueHammer PoC isn’t novel in concept—it’s a refined TOCTOU chain—but its timing, post-patch release, suggests either a gap in Microsoft’s root cause analysis or an intentional demonstration of patch fragility.”
From a deployment standpoint, the exploit requires no kernel access or driver signing bypass, making it particularly dangerous in environments where users retain local administrator privileges—a common configuration in development workstations and shadow IT scenarios. Benchmarks from internal red team tests indicate reliable exploitation across Windows 10 22H2 and Windows 11 23H2 with Defender definitions up to version 1.393.2508.0, with success rates exceeding 85% when executed via PowerShell or WScript. Notably, the PoC fails when Defender’s network inspection is enabled and SSL scanning is active, suggesting that deep packet inspection of loopback traffic may interrupt the file operation timing window—a potential mitigation vector for enterprises using Microsoft Defender for Business with advanced policies.
The exploit’s disclosure follows a pattern of increased tension between Microsoft and independent researchers over bounty eligibility and disclosure timelines. BlueHammer, previously associated with the release of CVE-2025-XXXXX (a PrintNightmare variant), claims the vulnerability was reported privately 90 days prior to public release but was dismissed as “low severity” due to Defender’s existing exploit guard mitigations. Whether this characterization was accurate remains debated, but the incident underscores the growing friction between vendor-led patch cycles and the exploit development community’s expectations for timely remediation. For organizations, this reinforces the need to treat endpoint protection platforms not as silver bullets but as one layer in a defense-in-depth strategy—particularly when facing adversaries who understand the inner workings of the extremely tools meant to stop them.
“Relying solely on AV/EDR for privilege escalation defense is like locking your front door but leaving the windows open. These logic flaws live in the gaps between assumed trust boundaries. Continuous validation—through red teaming, configuration audits, and exploit simulation—is non-negotiable.”
To detect potential exploitation attempts, defenders should monitor for anomalous hardlink creation events involving Defender’s quarantine directory (%ProgramData%\Microsoft\Windows Defender\Quarantine) and unusual parent-child process relationships where MsMpEng.exe spawns cmd.exe or powershell.exe with elevated privileges. A practical detection rule for Microsoft Sentinel or Azure Log Analytics appears below:
// KQL query to detect potential BlueHammer-style hardlink abuse in Defender Event | where EventID == 11 and TargetFilename has_any ("Quarantine", "wuauclt.exe") | where InitiatingProcessFileName in~ ("powershell.exe", "wscript.exe", "cscript.exe") | extend HardlinkDetected = iff(TargetFilename endswith ".dll" and FileAttributes contains "REPARSE_POINT", true, false) | where HardlinkDetected == true | project TimeGenerated, Computer, InitiatingProcessFileName, TargetFilename, InitiatingProcessAccountName Organizations lacking the telemetry depth for custom hunting should consider engaging managed service providers with SOC 2 Type II compliance to outsource threat detection and response tuning. Similarly, firms undergoing digital transformation or cloud migration can leverage software development agencies experienced in secure Windows service hardening to audit custom applications that may inadvertently increase Defender’s attack surface—such as those performing frequent file operations in system directories.
The broader implication is clear: as endpoint protection platforms grow more sophisticated, so too do the attacks that target their operational logic rather than their memory safety. The BlueHammer PoC serves as a reminder that trust boundaries in security software are not invariant—they are shaped by assumptions about file integrity, process lineage, and user intent, all of which can be manipulated when timing and context align. Until Microsoft publishes a root cause analysis confirming whether this represents a bypass, a variant, or a failure in exploit guard coverage, enterprises must assume active risk and validate their Defender configurations against known attack patterns—ideally with third-party verification.
*Disclaimer: The technical analyses and security protocols detailed in this article are for informational purposes only. Always consult with certified IT and cybersecurity professionals before altering enterprise networks or handling sensitive data.*
