
Judge halts Nexstar/Tegna merger after FCC let firms exceed TV ownership limit
Judge Halts Nexstar/Tegna Merger: A Circuit Breaker on Media Consolidation Risks
The U.S. District Court has issued a temporary restraining order against the Nexstar/Tegna merger, effectively hitting the emergency stop button on a deal that would have consolidated 265 TV stations under a single command structure. Judge Nunley’s ruling isn’t just about antitrust; it’s a recognition that creating a media monolith introduces a critical Single Point of Failure (SPOF) into the national broadcast infrastructure. For the CTOs and infrastructure architects watching this unfold, the takeaway is clear: centralization without redundancy is a vulnerability, not an efficiency gain.
- The Tech TL;DR:
- Infrastructure Risk: The merger would have created a “Sizeable Four” duopoly in 16 markets, reducing content diversity and increasing negotiation latency for distributors like DirecTV.
- Regulatory Patch: The “hold-separate” order acts as a temporary firewall, forcing Nexstar to maintain Tegna as an independent business unit with separate management and decision-making logic.
- Compliance Deadline: Nexstar must submit a compliance report by April 6, detailing how they are maintaining logical separation of assets—a classic audit requirement.
The Architecture of a Monopoly: Analyzing the Blast Radius
From a systems architecture perspective, the proposed merger looked like a classic vertical integration play that ignored the risks of coupling. Nexstar, already owning 201 stations, sought to absorb Tegna’s 64 stations. The plaintiff, DirecTV, argued that this consolidation would allow the merged entity to threaten blackouts, effectively holding content hostage during retransmission consent negotiations. What we have is analogous to a DDoS attack vector where a single provider controls the bandwidth for critical services.

The court’s decision to enforce a “hold-separate” order is essentially mandating a microservices architecture for the duration of the legal review. As noted in the ruling, Nexstar must permit Tegna to continue operating as a “separate and distinct, independently managed business unit.” This prevents the “swallowing” of assets that would eliminate head-to-head competition in 31 overlap markets. In the cybersecurity world, we observe similar patterns when organizations merge without proper segmentation; the blast radius of a single failure expands exponentially.
According to the Cybersecurity Risk Assessment and Management Services framework, identifying “irreparable harm” requires a structured analysis of potential failure points. DirecTV’s claim that they would suffer from “significantly diminished bargaining power” is a risk assessment conclusion: the merged firm would have too much leverage, creating a bottleneck in the content supply chain.
“When you consolidate control over critical infrastructure—whether it’s cloud compute or local news broadcasts—you introduce a systemic risk. The judge’s order is a manual override to prevent a monopoly from becoming a single point of failure for the entire market.”
Operational Segmentation: The “Hold-Separate” Protocol
The injunction details specific operational constraints that read remarkably like a security compliance checklist. Tegna leadership must maintain control over decision-making regarding “retransmission consent agreements, newsroom personnel, operations and programming.” This is not just legal jargon; it is a mandate for logical isolation. In IT terms, Nexstar is being forced to implement strict access controls and separation of duties to ensure Tegna remains an “economically viable, and active competitor.”
This level of oversight mirrors the responsibilities of a Director of Security at a major tech firm, where the goal is to ensure that integrated systems do not compromise the integrity of the whole. The requirement to maintain pre-merger staff levels is akin to ensuring service level agreements (SLAs) are met during a migration, preventing the degradation of service quality that often accompanies aggressive cost-cutting post-merger.
For enterprise IT leaders, the lesson here is about the complexity of M&A integration. Just as cybersecurity consulting firms advise on the risks of merging networks, this legal ruling highlights the need for rigorous Cybersecurity Audit Services to verify that separation is actually happening. You cannot just trust the merged entity to self-police; you need independent verification.
Implementation Mandate: Simulating Compliance Checks
To understand the technical rigor required to enforce such a “hold-separate” order, consider how an automated compliance script might verify the independence of two business units. Below is a conceptual Python script using a mock API to check for shared resources or cross-contamination of management decisions—a digital equivalent of the judge’s order.
import requests import json def audit_merger_separation(nexstar_api, tegna_api): """ Simulates a compliance check to ensure logical separation between Nexstar and Tegna assets per court order. """ headers = {'Authorization': 'Bearer COURT_ORDER_TOKEN'} # Check for shared newsroom personnel IDs nexstar_staff = requests.get(f"{nexstar_api}/v1/staff", headers=headers).json() tegna_staff = requests.get(f"{tegna_api}/v1/staff", headers=headers).json() shared_ids = set(nexstar_staff['ids']) & set(tegna_staff['ids']) if shared_ids: return { "status": "VIOLATION", "message": f"Shared personnel detected: {shared_ids}", "action": "Trigger Hold-Separate Alert" } # Check for unified retransmission consent logic nexstar_consent = requests.get(f"{nexstar_api}/v1/consent_logic", headers=headers).json() tegna_consent = requests.get(f"{tegna_api}/v1/consent_logic", headers=headers).json() if nexstar_consent['algorithm_hash'] == tegna_consent['algorithm_hash']: return { "status": "WARNING", "message": "Identical negotiation algorithms detected. Risk of collusion.", "action": "Require Algorithm Divergence" } return {"status": "COMPLIANT", "message": "Business units operate independently."} # Execution print(audit_merger_separation("https://api.nexstar.internal", "https://api.tegna.internal")) Risk Matrix: Consolidation vs. Segmentation
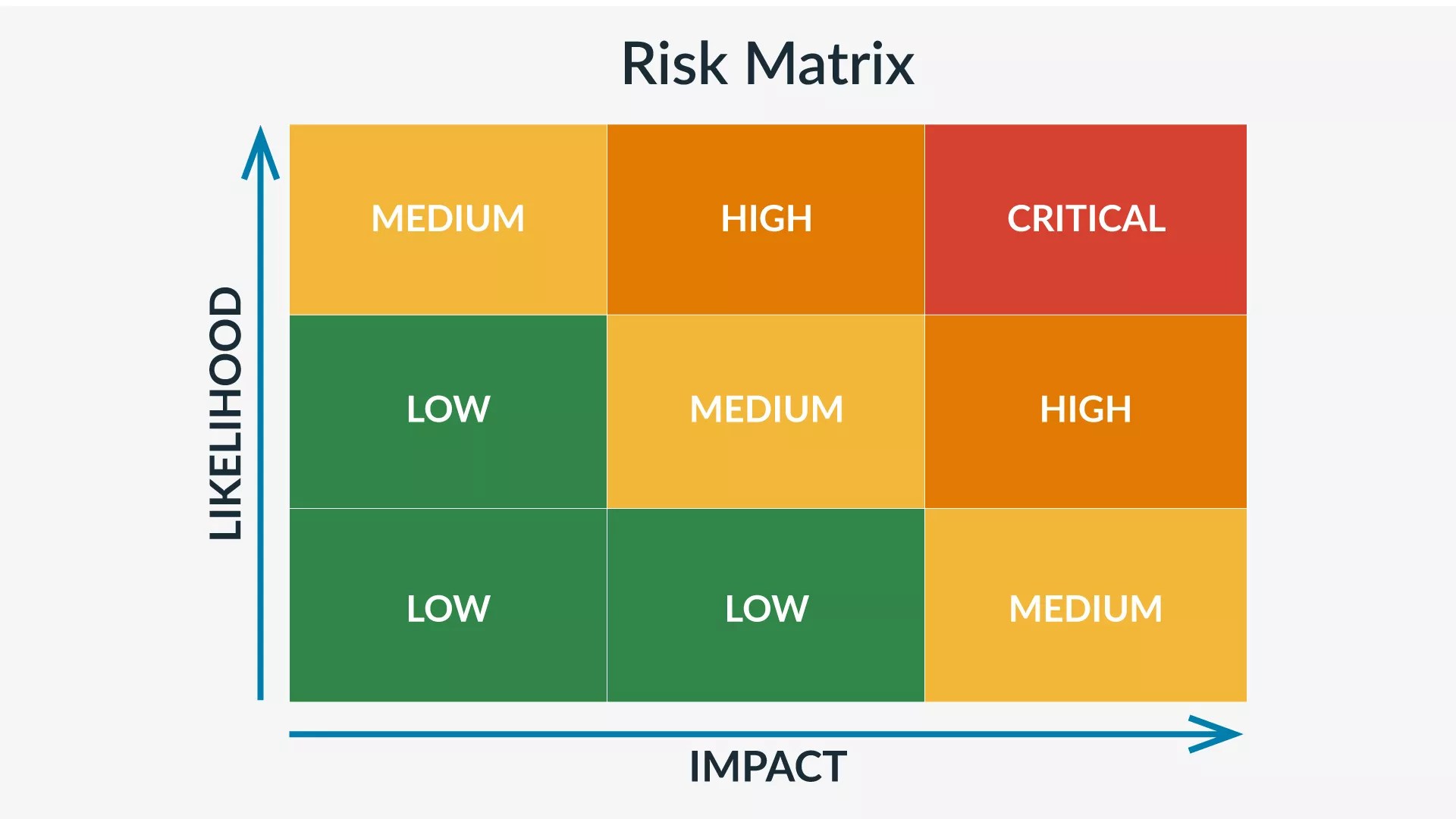
The following table breaks down the architectural differences between the proposed merger state and the court-mandated segmented state. This comparison highlights why the “monolith” approach poses a higher risk to market stability and content availability.
| Feature | Proposed Merger (Monolith) | Court-Ordered State (Segmented) | Risk Implication |
|---|---|---|---|
| Management Structure | Unified Command | Independent Business Units | High risk of coordinated blackouts vs. Competitive negotiation. |
| Newsroom Operations | Single News Director per Market | Separate News Personnel | Loss of editorial diversity; single point of content failure. |
| Retransmission Consent | Centralized Negotiation | Independent Negotiation | Monopoly pricing power vs. Market-driven rates. |
| Staffing Levels | Optimized/Reduced (Synergy) | Maintained Pre-Merger Levels | Operational resilience vs. Efficiency-driven fragility. |
The IT Triage: Why Auditors Matter in M&A
This legal battle underscores a broader truth for the technology sector: when large entities merge, the complexity of maintaining security and operational integrity skyrockets. Just as Nexstar is being forced to prove it isn’t absorbing Tegna, enterprises undergoing M&A need to engage cybersecurity auditors and penetration testers to ensure that the new combined network doesn’t inherit the vulnerabilities of the acquired company.
The “hold-separate” order is a temporary fix, much like a firewall rule that blocks traffic while a deeper vulnerability is patched. Long-term, the market needs robust mechanisms to ensure competition and diversity, similar to how we rely on Cybersecurity Consulting Firms to provide objective third-party validation of our security postures. Without independent oversight, the temptation to optimize for profit at the expense of resilience is too great.
As we wait for the April 7 hearing to discuss the potential preliminary injunction, the tech industry should watch closely. The principles of antitrust in media are increasingly aligning with the principles of decentralized architecture in software. Centralization creates fragility; segmentation creates resilience. Whether it’s a broadcast network or a cloud provider, the architecture of power matters.
Disclaimer: The technical analyses and security protocols detailed in this article are for informational purposes only. Always consult with certified IT and cybersecurity professionals before altering enterprise networks or handling sensitive data.
