‘It’s been a struggle’: Cryptocurrency scams on the rise as central Ohio man waits to get money back
The $10 Billion Latency Problem: Why Crypto Recovery Fails at the Protocol Level
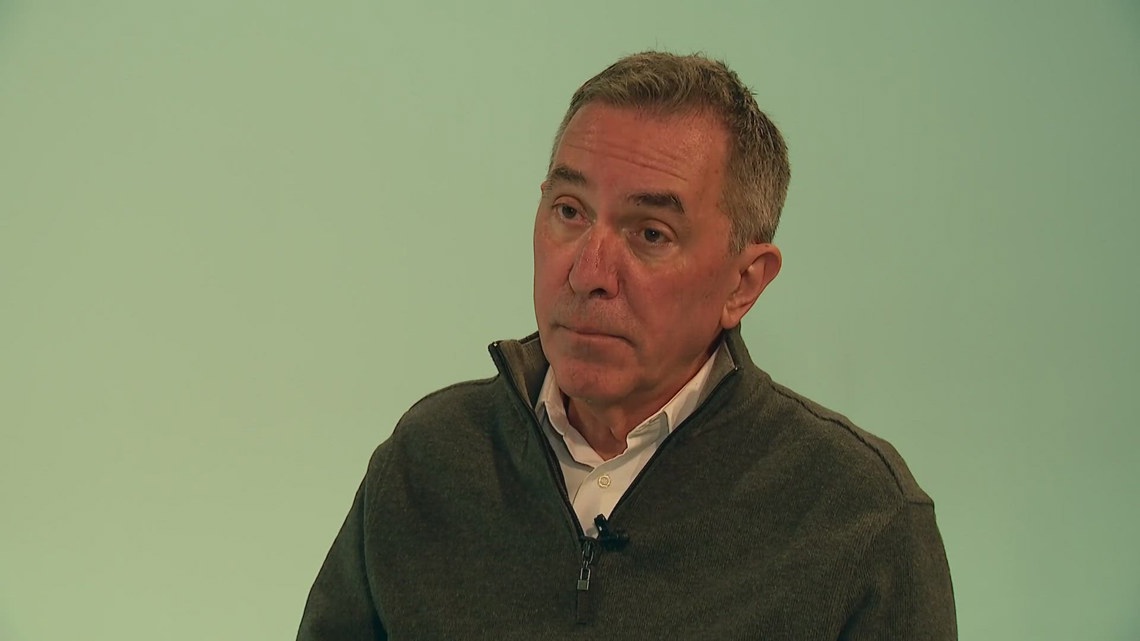
Dusty Frazier’s situation in central Ohio isn’t just a human interest story. it is a case study in forensic latency. Three years post-compromise, with $800,000 vanished into the blockchain ether, the delay isn’t bureaucratic inefficiency—it’s a fundamental architectural bottleneck in how we trace, seize, and remit digital assets. Whereas the U.S. Secret Service reports a $10 billion aggregate loss in 2024, the technical reality is that current recovery workflows operate on a timeline incompatible with the velocity of modern crypto-mixing services.
- The Tech TL;DR:
- Recovery SLA: Government forfeiture processes average 24+ months, far exceeding the liquidity window for most victims.
- Obfuscation Tech: Modern scams utilize chain-hopping and privacy coins (Monero/Zcash) to break heuristic tracing links within minutes.
- Enterprise Gap: Consumer-grade wallet security lacks the real-time anomaly detection found in AI-driven security landscapes used by institutional custodians.
The core issue facing victims like Frazier is the mismatch between immutable ledger technology and mutable legal processes. When a scammer executes a “rug pull” or social engineering attack, the assets move through a series of smart contracts and exchanges almost instantly. By the time a victim files an IC3 report and an agent is assigned, the funds have often passed through multiple tumblers. According to the AI Cyber Authority, the intersection of artificial intelligence and cybersecurity is evolving rapidly, yet consumer protection lags behind institutional defense mechanisms.
The Forensic Bottleneck: Heuristics vs. AI Agents
Traditional blockchain analysis relies on heuristic clustering—grouping addresses based on common spending patterns. This method is increasingly obsolete against adversarial AI agents designed specifically to generate noise and break these clusters. In 2026, we are seeing a shift toward behavioral biometrics and real-time transaction monitoring, similar to the security architectures being deployed by major tech firms to protect their own AI models.

The Secret Service’s admission that they handle hundreds of thousands of cases highlights a resource contention problem. From an engineering perspective, the “queue” for asset recovery is overloaded. While federal agents wait for judicial forfeiture, scammers are leveraging decentralized exchanges (DEXs) that require no KYC (Know Your Customer) verification. This creates a scenario where the “time-to-seize” is critically high, often resulting in total asset dissipation before legal mechanisms can freeze the endpoint.
“We use software tools that trace crypto through the blockchain, and we hope that it doesn’t get divided up into such small pieces that we can actually recover some of it.” — Morgan Morgan, Assistant to the Special Agent in Charge, U.S. Secret Service.
This reliance on “hope” is unacceptable in a zero-trust architecture. Enterprise environments do not hope; they verify. The disparity between consumer vulnerability and enterprise resilience suggests a market failure that specialized cybersecurity auditors are beginning to address. These firms utilize proprietary graph analysis tools that outpace standard law enforcement software, offering a potential parallel track for asset recovery.
Implementation: The Reality of On-Chain Tracing
Understanding why recovery fails requires looking at the code. Most victims do not realize that once a transaction is broadcast to the mempool, it is effectively irreversible unless the miner (or validator) has not yet confirmed it—a window of mere seconds. Below is a simplified Python snippet using web3.py demonstrating how a basic transaction trace works. In a real-world forensic scenario, this logic is expanded to traverse thousands of hops across multiple chains.
from web3 import Web3 # Connect to an Ethereum node (e.g., Infura or Alchemy) w3 = Web3(Web3.HTTPProvider('https://mainnet.infura.io/v3/YOUR_API_KEY')) def trace_funds(tx_hash): """ Basic recursive tracer to identify immediate output addresses. In production, this requires indexing services like The Graph or proprietary heuristics to handle internal transactions. """ tx = w3.eth.get_transaction(tx_hash) print(f"Tracing TX: {tx_hash}") print(f"From: {tx['from']} -> To: {tx['to']}") # Check receipt for internal contract interactions receipt = w3.eth.get_transaction_receipt(tx_hash) if receipt['status'] == 1: print("Transaction Successful. Funds moved to contract or EOA.") # Logic to parse logs for Transfer events would move here else: print("Transaction Reverted. Funds likely still in source wallet.") # Example usage for a suspected scam transaction # trace_funds('0x...') As demonstrated, even basic tracing requires API access to node infrastructure and the ability to parse complex event logs. For a victim like Frazier, this technical barrier is insurmountable without professional intervention. What we have is where the digital asset recovery specialists listed in our directory become critical. They possess the node infrastructure and heuristic databases necessary to identify “dust” attacks and peeling chains that standard tools miss.
The Economic Cost of Waiting
The “two-year” timeline cited by federal investigators is a lifetime in crypto volatility. If the seized assets are held in the original token (e.g., Bitcoin or Ethereum), market fluctuations can render the recovered amount negligible by the time the regulatory frameworks allow for remission. The legal process of “petition for remission” assumes the funds are still in a controlled wallet. In reality, sophisticated actors migrate funds to cold storage or convert them to fiat via offshore OTC (Over-The-Counter) desks within hours.
Dr. Elena Rostova, a lead researcher at the Synopsys Software Integrity Group, notes the shifting landscape: “The complexity of these scams now rivals state-sponsored APT (Advanced Persistent Threat) campaigns. We are seeing social engineering scripts generated by LLMs that are indistinguishable from human support agents, lowering the barrier to entry for scammers while raising the technical bar for defenders.”
For the enterprise, the solution lies in proactive defense—implementing AI-driven security layers that flag suspicious transaction patterns before the user authorizes the transfer. For the consumer, however, the options are reactive and grim. The reliance on law enforcement as the primary recovery vector is a single point of failure. A diversified approach involving immediate engagement with incident response teams offers the only statistical probability of intercepting funds before they vanish into the deep web.
As we move further into 2026, the distinction between “cybersecurity” and “financial security” will dissolve. The architecture of trust is being rewritten, and those who rely on legacy recovery methods will continue to face the same heartbreaking latency that Dusty Frazier endures today. The technology to prevent these losses exists; the challenge is deploying it at the edge, where the user interacts with the chain.
Disclaimer: The technical analyses and security protocols detailed in this article are for informational purposes only. Always consult with certified IT and cybersecurity professionals before altering enterprise networks or handling sensitive data.
