Google Unusual Traffic From Your Computer Network Error Explained
Global digital infrastructure faced unprecedented strain on March 26, 2026, as automated network traffic surged across major nodes in North America, and Europe. This event, characterized by a massive spike in non-human requests, has triggered widespread service outages and raised immediate concerns regarding data sovereignty and municipal network security protocols.
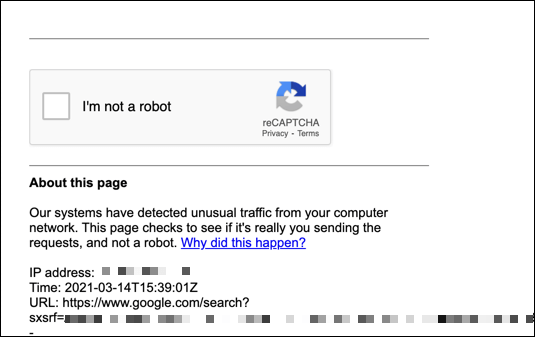
The digital landscape shifted violently this morning. What began as a routine Tuesday for millions of remote workers and municipal administrators dissolved into a cascade of connection timeouts and security blocks. By 19:00 UTC, major search engines and content delivery networks began flagging legitimate user traffic as “unusual,” effectively locking out vast swathes of the public from essential digital services.
This is not merely a technical glitch. It is a symptom of a deeper, systemic fragility in our 2026 connectivity model.
As the dust settles on this digital blackout, the immediate problem for citizens and businesses is clear: access denial. When the gatekeepers of the internet—search algorithms and security firewalls—mistake human activity for bot attacks, commerce stops. Legal compliance becomes a guessing game. For local municipalities relying on cloud-based governance tools, the paralysis is total.
The Anatomy of the March 26 Traffic Surge
Initial forensic analysis suggests the surge originated from a distributed network of compromised IoT devices, specifically targeting the authentication layers of major tech conglomerates. Unlike the ransomware attacks of the early 2020s, this event was a Denial of Service via “False Positive” flooding. The systems didn’t crash; they locked down.

The implications for local governance are severe. Cities that migrated their permitting, emergency response, and utility billing to centralized cloud platforms are now facing a logistical nightmare. The “Terms of Service” violations detected by automated systems are not malicious acts by citizens, but collateral damage of a broader network war.
“We are seeing a fundamental breakdown in the trust layer of the internet. When a municipal server blocks a citizen’s IP address because it looks like a robot, we aren’t just losing data; we are losing civic access. This requires immediate legal and technical intervention.” — Dr. Elena Rostova, Senior Fellow at the Geneva Institute for Cyber-Diplomacy
The geographic impact is uneven. While major hubs like London and New York have redundant fiber lines that absorbed some of the shock, mid-sized jurisdictions relying on single-provider 5G backhauls are experiencing total blackouts. In these regions, the inability to verify identity online has stalled everything from hospital admissions to property transfers.
Immediate Risks and The Directory Solution
For business owners and property managers, the risk profile has changed overnight. The “Unusual Traffic” errors are often precursors to actual data exfiltration attempts. If your network was flagged today, your perimeter may already be compromised.
The solution requires a two-pronged approach: immediate technical hardening and legal risk mitigation.
First, organizations must audit their external-facing ports. The automated scripts driving this traffic are evolving rapidly. Relying on legacy firewalls is no longer sufficient. Entities facing persistent connection drops need to engage with specialized network security firms capable of distinguishing between legitimate high-volume traffic and malicious botnets. These professionals can implement behavioral analysis tools that white-list human users even during a surge.
Second, the legal ramifications are complex. If your business data was inaccessible during this window, causing breach of contract with clients, you are entering a liability gray area. Force Majeure clauses are being tested in real-time. Corporations are advised to consult with technology liability attorneys immediately to document the outage and shield assets from potential litigation arising from service failures.
Comparative Impact: Infrastructure Resilience by Region
The disparity in how different regions handled the March 26 surge highlights the urgent need for infrastructure investment. The following data compares the recovery times and impact levels across key jurisdictions.
| Region | Primary Impact | Recovery Time (Est.) | Critical Vulnerability |
|---|---|---|---|
| North America (Urban) | Search Engine Lockouts | 4-6 Hours | Over-reliance on Single-Provider DNS |
| European Union | GDPR Compliance Flags | 12-24 Hours | Automated Privacy Filtering False Positives |
| Asia-Pacific | Mobile Data Throttling | 2-4 Hours | 5G Spectrum Congestion |
| Emerging Markets | Total Service Blackout | 48+ Hours | Lack of Redundant Fiber Backhaul |
As the table illustrates, the “digital divide” is no longer just about access; it is about resilience. Regions with diversified infrastructure recovered significantly faster. For local governments in the “Emerging Markets” category, the path forward involves heavy capital investment in telecommunications infrastructure developers to build redundant, decentralized networks that can withstand automated flooding.
The Long-Term Shift: From Automation to Verification
The events of March 26, 2026, will likely be remembered as the turning point where the internet stopped trusting automation. We are moving toward an era of “Zero-Trust Architecture,” where every request, human or machine, must be rigorously verified.
This shift creates a massive demand for compliance experts. As new regulations emerge to govern bot traffic and network attribution, businesses will need guidance. The regulatory compliance sector is poised to grow the most critical service industry of the late 2020s.
We are standing on the precipice of a new digital reality. The tools we built to connect the world are now the weapons used to disconnect it. The question is no longer “How fast can we go?” but “How securely can we verify?”
For those navigating this turbulent landscape, the World Today News Directory remains your anchor. We connect you not just with the news, but with the verified global professionals who can rebuild the infrastructure of trust, one secure connection at a time.
