Engineer Brings Lightning Port to iPhone 17 Pro
Reverse Engineering the Lightning Port on iPhone 17 Pro: A Security Post-Mortem
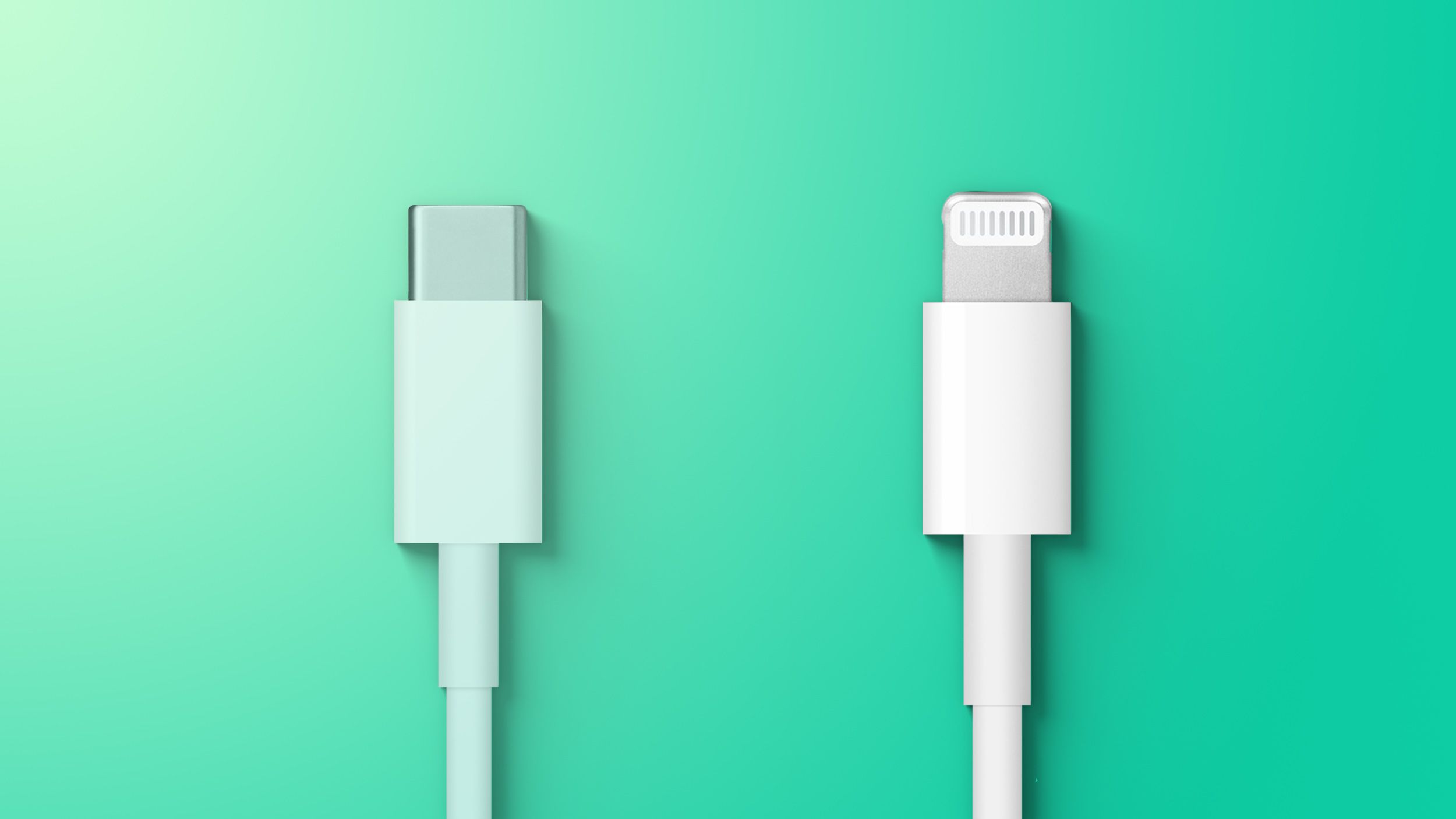
Ken Pillonel, the Swiss robotics engineer known for forcing USB-C onto Lightning iPhones, has inverted the workflow. As of April 1, 2026, he has deployed a functional Lightning port on the USB-C native iPhone 17 Pro. While marketed as a tongue-in-cheek prototype, this hardware mod exposes significant attack vectors in physical interface translation. For enterprise security teams, this isn’t a novelty; it is a proof-of-concept for legacy protocol tunneling on modern secured hardware.
- The Tech TL;DR:
- Attack Surface: Custom PCBs bridging Lightning and USB-C introduce potential man-in-the-middle (MitM) vulnerabilities during power negotiation.
- Compliance Risk: Modifying certified hardware voids UL safety ratings and violates corporate MDM policies regarding unauthorized peripherals.
- Deployment Reality: No commercial availability; although, the design files highlight gaps in supply chain cybersecurity for third-party accessories.
The build relies on a custom PCB for connector placement, housed in a flexible TPU case printed on a Formlabs SLS machine. Pillonel utilized a magnet installation jig fabricated on a Prusa printer to ensure MagSafe alignment. While the assembly is snap-fit and slim, the underlying architecture requires active protocol translation. The iPhone 17 Pro expects USB Power Delivery (PD) negotiation, while the Lightning interface operates on Apple’s proprietary protocol stack. This mismatch creates a latency bottleneck and a potential voltage regulation failure point.
Protocol Mismatch and Voltage Regulation Risks
Hardware mods of this nature bypass the device’s internal power management integrated circuit (PMIC) safeguards. When a legacy Lightning connector is forced onto a USB-C controller, the negotiation handshake occurs externally on the modded PCB. If the translation layer fails to correctly interpret the USB-PD 3.1 specification, the device risks receiving incorrect voltage rails. In a production environment, this translates to thermal throttling or permanent battery degradation.

Enterprise IT departments cannot treat this as an isolated hobbyist project. The availability of open-source design files means malicious actors could replicate the PCB layout without the safety constraints Pillonel implemented. Organizations relying on cybersecurity audit services must now include physical port inspection in their endpoint compliance checks. The risk isn’t just data exfiltration; it is physical hardware damage via over-voltage.
Developers analyzing the USB protocol stack should reference the official USB Power Delivery Specification to understand the expected handshake sequences. Deviations from these standards in third-party accessories often indicate poor engineering or intentional backdoors. For those inspecting device power states, the following CLI command retrieves current power delivery stats on macOS-based management stations:
ioreg -l | grep -i "PowerDelivery" | awk '{print $2, $4}'This command filters the I/O Registry for power delivery instances, allowing admins to spot anomalies in voltage negotiation logs. Unexpected values here often correlate with non-compliant hardware accessories.
Supply Chain Implications and Third-Party Risk
The existence of such mods underscores the fragility of hardware supply chains. When organizations depend on third-party vendors for accessories, they introduce unverified components into their secure perimeter. This aligns with findings from Supply Chain Cybersecurity Services providers, who note that hardware modifications are a growing vector for introducing persistent threats.
A modified case is not just a plastic shell; it is an embedded system. The PCB inside Pillonel’s case acts as an intermediary. If a bad actor compromises the firmware on such a bridge, they could intercept data traffic or inject malicious payloads before they reach the device’s secure enclave. This is why supply chain cybersecurity services are critical for enterprises procuring hardware peripherals. Verification must extend beyond the device itself to every connected component.
“Physical access is the ultimate privilege escalation. Adding a legacy port to a modern device creates a translation layer that bypasses native hardware security checks. We treat these mods as untrusted peripherals by default.” — Senior Mobile Forensic Researcher, Global Incident Response Team
The security community generally agrees that hardware modifications void the trust model of the device. According to the libimobiledevice repository documentation, communicating with iOS devices over non-standard interfaces requires bypassing standard authentication flows. This increases the likelihood of triggering security alerts or locking the device into recovery mode.
Compliance and Corporate Policy Enforcement
For CTOs managing fleets of iPhone 17 Pros, this mod represents a policy enforcement challenge. Mobile Device Management (MDM) solutions often flag unauthorized accessories, but they cannot always detect physical hardware modifications that do not require software installation. This gap necessitates a shift toward physical security audits.

Companies should engage cybersecurity consulting firms to update their acceptable employ policies. These policies must explicitly forbid hardware modifications that alter input/output interfaces. The cost of a compromised endpoint far outweighs the convenience of legacy connector compatibility. Insurance policies covering hardware damage often exclude incidents resulting from unauthorized modifications.
Technical leaders must also consider the latency implications. Protocol translation adds processing overhead. In high-frequency trading or real-time data capture scenarios, the microsecond delays introduced by an external bridge could violate SLA requirements. Benchmarking tools like Geekbench do not measure I/O latency introduced by external hardware, leaving a blind spot in performance monitoring.
The Verdict on Hardware Modding
Pillonel’s project is a engineering marvel but a security nightmare. It demonstrates that physical constraints are merely suggestions to skilled engineers, but for enterprise security, they are hard boundaries. The ability to revert a USB-C port to Lightning proves that hardware standards are permeable. This permeability is what Cybersecurity Consulting Firms warn against when defining secure perimeters.
As we move deeper into 2026, the line between hardware and software security continues to blur. The iPhone 17 Pro Lightning mod is a reminder that physical access controls remain paramount. Organizations must prioritize Cybersecurity Audit Services that include physical inspections of employee devices. Relying solely on software-based MDM is insufficient when the hardware itself can be rewritten.
The trajectory is clear: hardware security will grow as critical as network security. Expect to see more rigorous certification requirements for accessories in corporate environments. The era of plug-and-play trust is ending, replaced by zero-trust hardware architectures.
Disclaimer: The technical analyses and security protocols detailed in this article are for informational purposes only. Always consult with certified IT and cybersecurity professionals before altering enterprise networks or handling sensitive data.
