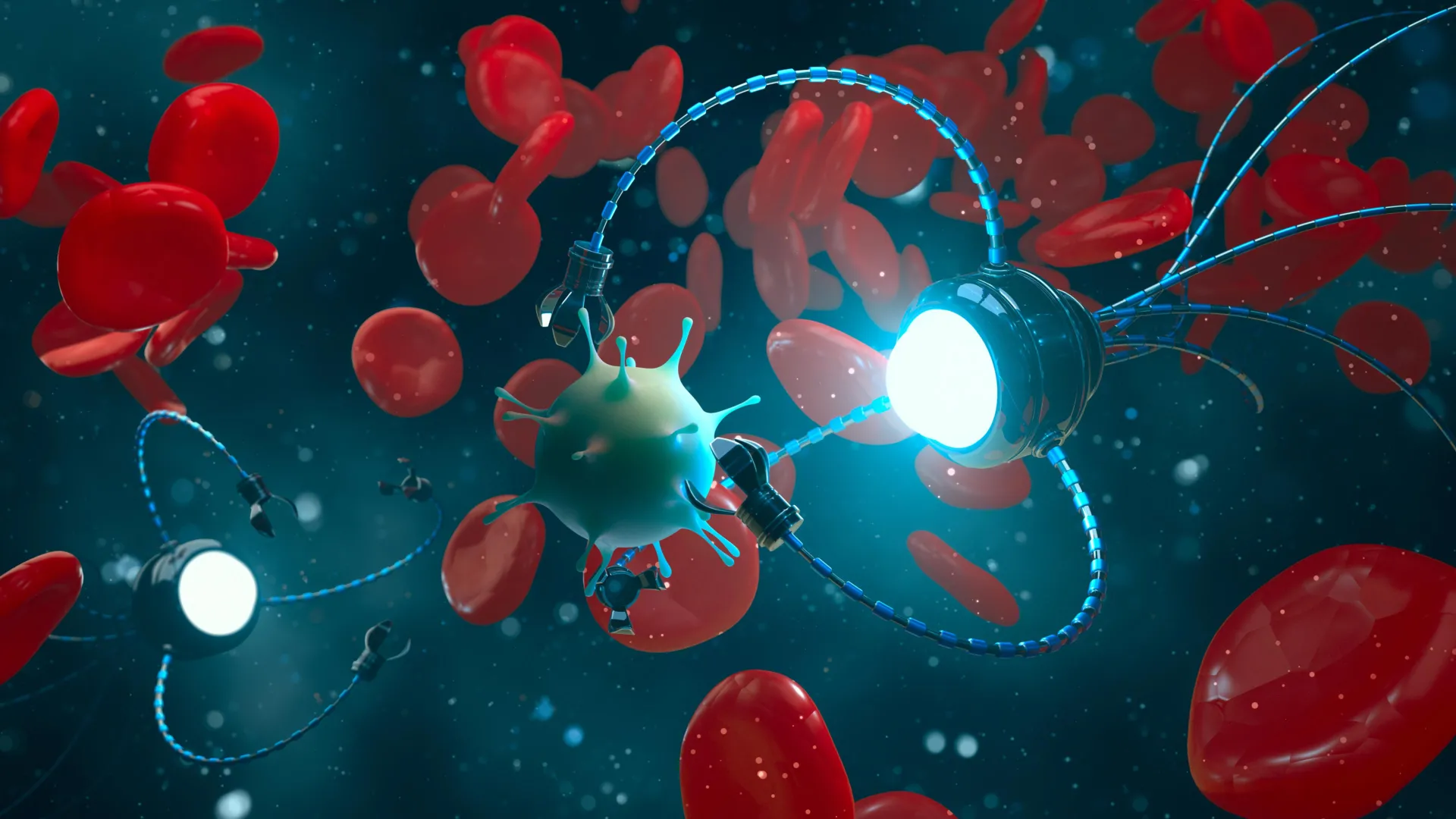
DNA robots could deliver drugs and hunt viruses inside your body
Bio-Computing Endpoints: The Security Debt of DNA Nanorobotics
The promise of DNA nanorobots hunting viruses inside the human bloodstream sounds like science fiction until you realize the command-and-control infrastructure doesn’t exist. We are building molecular machines capable of autonomous drug delivery without establishing a zero-trust architecture for the biochemical signals that drive them. Although research teams celebrate proof-of-concept strides in origami folding and strand displacement, the industry is ignoring the attack surface these devices create. If a bad actor intercepts the “fuel” sequence, they don’t just stop the robot. they weaponize it.
- The Tech TL;DR:
- DNA robots currently lack standardized authentication protocols for biochemical commands, creating a high-risk vector for unauthorized drug delivery.
- Control systems rely on external fields (magnetic/light) that are susceptible to interception or spoofing without encryption layers.
- Enterprise adoption requires immediate engagement with cybersecurity auditors specializing in emerging bio-digital interfaces.
Engineering motion at the nanoscale introduces latency issues that traditional IT security models cannot parse. The primary mechanism for controlling these machines, DNA strand displacement, functions like a biochemical API. Specific sequences labeled as “fuel” trigger structural changes. Yet, unlike a REST API secured by OAuth2, these molecular endpoints operate in the open environment of the human body. Brownian motion adds noise to the signal, requiring higher energy inputs that can be detected and potentially jammed. This isn’t just a stability issue; We see a confidentiality and integrity failure waiting to happen.
The Control Plane Vulnerability
Current designs operate in isolation, lacking the telemetry required for modern security operations centers. When researchers discuss using electric or magnetic fields to direct movement, they are essentially broadcasting control signals over unencrypted channels. In a clinical setting, this equates to sending admin credentials over HTTP. The AI Cyber Authority notes that rapid technical evolution in AI sectors often outpaces regulatory frameworks, a gap that is even wider in bio-computing. Without a standardized protocol for verifying the source of a molecular command, any entity with the correct sequence syntax could trigger a payload.

Consider the deployment lifecycle. A DNA robot designed to target cancer cells must distinguish between healthy and diseased tissue based on molecular markers. If the logic governing this distinction is flawed or spoofed, the robot becomes a toxin delivery system. This mirrors the challenges faced in AI security, where adversarial inputs can manipulate model behavior. Just as Microsoft AI is hiring leadership to secure intelligent systems, the bio-tech sector needs equivalent oversight for programmable matter. The convergence of AI design and DNA fabrication means the security posture of the software directly dictates the safety of the hardware.
Architectural Comparison: Control Methodologies
To understand the risk profile, we must evaluate the current control mechanisms against security standards. The following breakdown compares the prevalent methods for guiding DNA robots against enterprise security requirements.
| Control Method | Latency | Encryption Potential | Attack Vector |
|---|---|---|---|
| DNA Strand Displacement | High (Biochemical) | Low (Sequence Obfuscation) | Sequence Interception |
| Magnetic Fields | Low (Physical) | None (Broadcast) | Signal Spoofing |
| Light Activation | Medium | Medium (Frequency Keying) | Optical Jamming |
The data indicates that strand displacement, while precise, offers the lowest inherent security. It relies on the secrecy of the sequence, which violates Kerckhoffs’s principle. Security should not depend on the obscurity of the design. As the AI Security Category Launch Map highlights, the market is flooding with vendors addressing AI vulnerabilities, yet none currently cover bio-digital interfaces. This gap leaves early adopters exposed.
Implementation Mandate: Securing the Payload
Developers working on nanobot control interfaces must implement strict authentication before deploying commands to physical hardware. Below is a conceptual example of how a secure payload request should be structured, ensuring that only authorized clinicians can trigger specific molecular actions. This mimics the rigor required in Synopsys AI Strategy roles, where software integrity is paramount.
curl -X POST https://api.bio-control.internal/v1/execute -H "Authorization: Bearer <CLINICIAN_TOKEN>" -H "Content-Type: application/json" -d '{ "robot_id": "DNA-NANO-774", "action": "RELEASE_PAYLOAD", "target_marker": "EGFR+", "signature": "sha256_verified_sequence_hash" }' This API structure enforces identity management at the point of care. Without this layer, the physical act of drug delivery remains unauthenticated. Organizations integrating these systems should immediately consult with cybersecurity consultants to audit their bio-digital interfaces. The Security Services Authority emphasizes the need for verified service providers to manage such regulatory frameworks. Ignoring this triage step invites liability.
“The robots of tomorrow won’t just be made of metal and plastic. They will be biological, programmable, and intelligent. But without a security layer, they are just uncontrolled variables in a closed system.” — Lead Researcher, Institute for Molecular Manufacturing
Scaling these systems requires more than just better folding techniques; it demands a shift in how we view biological endpoints. The industry is currently treating DNA robots as hardware, but they are effectively distributed software running on wetware. This distinction matters for compliance. SOC 2 frameworks do not yet account for molecular data storage or programmable viruses. Until standards catch up, the burden falls on engineering teams to implement defense-in-depth strategies.
The Path Forward
Collaboration across disciplines is not just a suggestion; it is a requirement for survival. Creating standardized DNA “parts libraries” without security metadata is negligence. AI must be used to simulate attacks on these structures before they enter production environments. We need to see the same level of scrutiny in bio-computing that we currently apply to cloud infrastructure. As enterprise adoption scales, the cost of a breach shifts from data loss to physical harm.
For CTOs evaluating this technology, the directive is clear: do not deploy without a security audit. Engage managed service providers who understand both the biochemical and digital attack surfaces. The future of medicine depends on our ability to secure the code that writes itself inside the human body.
Disclaimer: The technical analyses and security protocols detailed in this article are for informational purposes only. Always consult with certified IT and cybersecurity professionals before altering enterprise networks or handling sensitive data.
