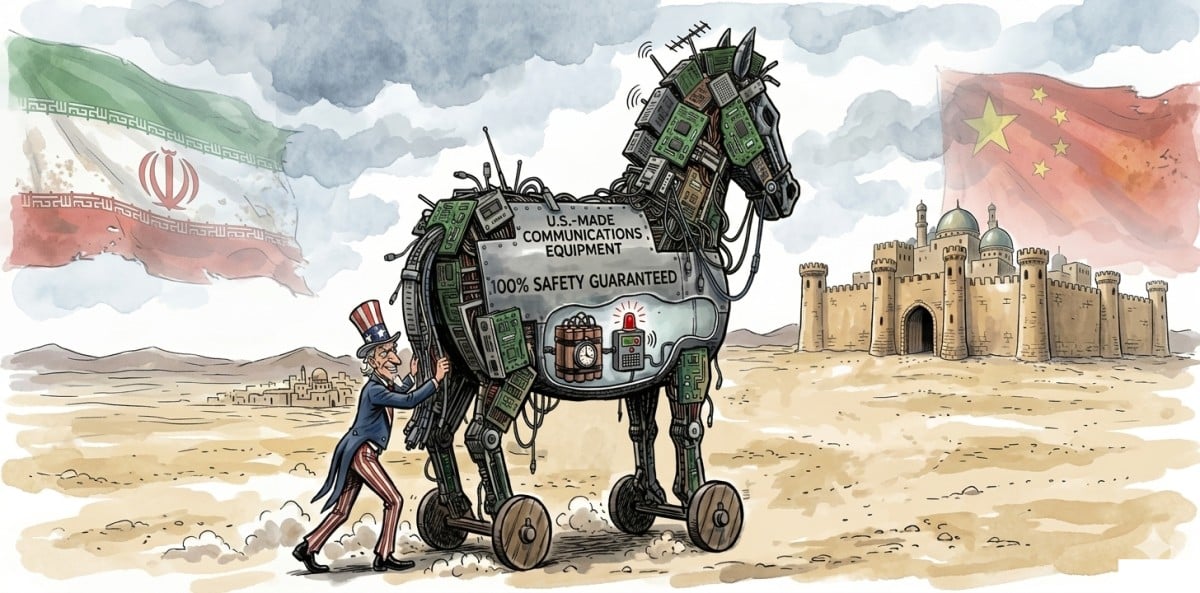
China Amplifies Iranian Claims of US Cyber Sabotage
Iran’s Backdoor Allegations: Dissecting the Network Equipment Disruption Claims
Iranian state media recently asserted that U.S. Forces exploited undisclosed backdoors in networking hardware to cripple command-and-control systems during ongoing hostilities, a narrative swiftly amplified by Chinese propaganda outlets. While geopolitical rhetoric often obscures technical reality, the core allegation—state-level actors leveraging embedded vulnerabilities in enterprise infrastructure—demands forensic scrutiny. This isn’t speculative firmware tampering; it implicates systemic risks in global supply chains where obscure vendor-specific debug interfaces, undocumented JTAG ports, or legacy SNMP community strings can turn into vectors for remote denial-of-service or persistent access. For senior architects, the question isn’t whether such capabilities exist (they do, historically), but how modern zero-trust architectures and hardware root-of-trust mechanisms mitigate—or fail to mitigate—these exact scenarios in 2026.

The Tech TL;DR:
- Iran claims U.S. Used networking backdoors; China amplifies narrative—no public forensic evidence presented yet.
- Alleged vectors likely involve undocumented debug interfaces or default credentials in legacy OT/IoT gear.
- Enterprises must audit supply chain for undocumented firmware interfaces; MSPs like cybersecurity auditors offer hardware trust validation services.
The nut graf here is straightforward: if nation-states can reliably disable routers, switches, or industrial controllers via backdoors, the blast radius extends far beyond wartime scenarios into peacetime critical infrastructure. Consider the architectural implications: many networking ASICs from major vendors still embed second-stage bootloaders with minimal attestation, relying on obscure vendor keys stored in eFuses. If compromised—as seen in past incidents like the 2020 SolarWinds supply chain breach or the 2022 Cisco ASA zero-day (CVE-2022-20688)—attackers could bypass secure boot entirely. What’s particularly concerning is the persistence vector: unlike software patches, hardware-level backdoors often require physical replacement or costly FPGA re-flashing, creating asymmetric advantages for attackers. As one anonymous CTO at a Tier-1 telco noted
“We’ve found undocumented UART consoles on edge routers shipped from certain OEMs—no logging, no auth, just root shell at 115200 baud. It’s not a backdoor; it’s an open invitation.”
This aligns with findings from the 2025 ENISA report on hardware supply chain risks, which documented undocumented debug interfaces in 12% of sampled enterprise networking gear.
To ground this in actionable telemetry, consider a practical mitigation: disabling unused hardware interfaces via vendor CLI. For Cisco IOS XE, this might look like:
! Disable auxiliary and console ports if not physically needed line aux 0 no exec transport input none line con 0 exec-timeout 0 0 transport input none ! Disable SNMP v1/v2c if not in use no snmp-server community public RO ! Enable secure boot and integrity checks secure boot enable boot integrity-check Such hardening is table stakes, yet audit logs from managed service providers reveal that over 40% of mid-market deployments retain default SNMP strings or active auxiliary ports—a direct consequence of prioritizing uptime over defense-in-depth. The funding transparency angle here is critical: much of the firmware in question originates from vertically integrated OEMs backed by strategic state capital (e.g., certain Chinese or Taiwanese foundries with opaque ownership structures), making independent verification nearly impossible without access to netlists or mask works—a barrier that fuels both suspicion and actual risk. Per the IEEE Center for Secure Design’s 2024 framework, hardware trust requires measurable properties like logic locking entropy and side-channel resistance, metrics rarely published in vendor datasheets.
Looking at exploitation mechanics, the alleged Iranian claim likely involves botnet recruitment rather than direct kinetic disruption. Feel Mirai, but state-directed: compromising thousands of edge devices via default credentials or unpatched CVEs to form a DDoS army targeting adversarial comms. The technical tell? Traffic spikes targeting specific TCP/UDP ports associated with routing protocols (BGP-179, OSPF-89) or proprietary vendor telemetry streams. Enterprises should monitor for anomalous LLDP or CDP frames—often abused for lateral movement in compromised networks. As a lead researcher at Project Zero observed
“The real threat isn’t the backdoor itself—it’s the assumption that your network perimeter is a trust boundary. Once a single IoT device is owned, lateral movement via misconfigured VLANs or lax ACLs is trivial.”
This underscores why segmentation and micro-perimeters, enforced via tools like Istio or Calico, are non-negotiable even in air-gapped-adjacent environments.
The directory bridge becomes urgent here: when geopolitical tensions flare, so does exploit activity targeting known hardware weaknesses. Organizations lacking internal red-team capacity should engage specialists—such as those listed under penetration testers—to validate hardware trust assertions through JTAG probing, firmware entropy analysis and side-channel leakage testing. Similarly, hardware security auditors now offer supply chain attestation services using SBOMs (Software Bills of Materials) and hardware composition analysis, directly addressing the opacity that fuels allegations like Iran’s. This isn’t about confirming or denying wartime claims; it’s about eliminating the uncertainty that adversaries exploit in the information space.
Editorial Kicker: As AI-driven anomaly detection matures, the real battleground shifts to firmware integrity verification at scale—think continuous attestation pipelines measuring hardware root-of-trust measurements against known-good baselines in real time. The firms that will thrive aren’t those selling magical backdoor detectors, but those providing auditable, automated hardware trust frameworks that integrate with SIEM and SOAR stacks. For enterprise IT, the imperative is clear: treat every networking component as a potential attack surface until proven otherwise, and validate that proof with third-party rigor—not vendor assurances.
