The Data Access Crisis: Why Network Latency is the New Liquidity Trap
Global financial markets are facing a silent erosion of efficiency as automated bot traffic and network congestion trigger widespread data access failures, forcing institutional investors to confront a new reality where information latency directly translates to capital loss. This infrastructure fragility, highlighted by recent systemic blocks on major data portals, demands immediate investment in enterprise-grade network security and redundancy protocols to safeguard asset valuation.
We treat a “403 Forbidden” or a “Unusual Traffic Detected” error as a minor annoyance. On the trading floor, it is a liquidity event. When a network node flags legitimate high-frequency queries as malicious, the resulting blackout creates an information asymmetry that arbitrageurs exploit instantly. The error message displayed on standard search interfaces today—blocking access to critical video briefings and market data due to “automated requests”—is not a glitch. It is a symptom of a saturated digital supply chain.
In the first quarter of 2026, we are seeing a divergence between asset value and data accessibility. The problem is fiscal: every second of latency caused by security handshakes or bot mitigation filters represents a slippage in execution price. For mid-cap firms relying on real-time sentiment analysis from platforms like YouTube or specialized financial feeds, the inability to ingest data due to IP throttling is a direct hit to EBITDA. The market is pricing in risk, but it is underpricing the cost of access.
This represents where the B2B landscape shifts. We are no longer just buying software; we are buying clearance. Firms that fail to integrate enterprise-grade network optimization services are effectively operating with blinders on. The solution lies not in avoiding security, but in whitelisting institutional traffic through verified channels that distinguish between a DDoS attack and a legitimate algorithmic query.
The Macro Shift: Three Structural Changes for Q2 2026
The incident involving the blocking of standard financial content due to “unusual traffic” signals a broader tightening of the digital perimeter. We are moving from an open internet model to a gated community model for high-value data. Here is how this alters the investment thesis for the coming fiscal year:
- The Premium on Verified Identity: Anonymous scraping is dead. Institutional access will soon require cryptographic proof of identity at the network layer. Firms must consult with digital identity compliance specialists to ensure their data ingestion pipelines are not flagged as hostile actors. The cost of non-compliance is no longer a fine; it is total data blackout.
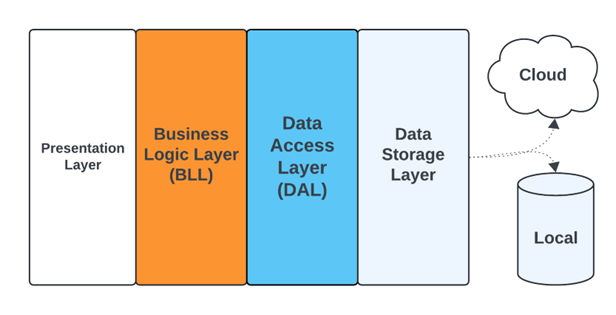
- Decentralized Data Redundancy: Relying on a single IP range for market intelligence is now a single point of failure. Treasury departments must allocate capital toward distributed network architectures. This isn’t just IT spend; it is risk mitigation. The firms winning in 2026 are those treating bandwidth diversity with the same rigor as currency hedging.
- The Rise of “Clean” Data Providers: As raw data sources become clogged with bot-mitigation friction, the value of aggregated, pre-cleaned data feeds skyrockets. We expect a consolidation wave where data aggregators who maintain pristine reputational scores with search giants acquire significant pricing power.
Consider the margin impact. If a quantitative fund loses 15 minutes of data ingestion daily due to network throttling, the alpha decay is measurable. In a market moving at microsecond speeds, a 15-minute lag is an eternity. This forces a re-evaluation of vendor contracts. Are your data providers guaranteeing uptime, or just availability? There is a difference.
“We are seeing a fundamental breakdown in the trust layer of the internet. For financial institutions, the ‘captcha’ is the new border control. If you cannot prove you are human—or rather, a legitimate entity—without friction, you are locked out of the market.”
This sentiment, echoed by senior infrastructure architects at major cloud providers, underscores the urgency. The “unusual traffic” warning is a canary in the coal mine for a broader crackdown on unverified data flows. It suggests that the major platforms are deploying aggressive AI-driven defense mechanisms that lack nuance, catching legitimate corporate research tools in the crossfire.
The fiscal implication is clear: Operational expenditure (OpEx) for IT security must rise to protect Revenue. Companies necessitate to audit their external facing IP addresses. Are they shared? Are they on blacklists? A shared corporate network, as hinted in the error diagnostics (“If you share your network connection…”), is a liability. In 2026, a dedicated fiber line for market data isn’t a luxury; it’s a regulatory necessity for fiduciary duty.
this environment creates a lucrative niche for corporate law firms specializing in digital access rights. We anticipate litigation regarding “unfair blocking” of institutional data. If a platform’s algorithm erroneously blocks a hedge fund’s research arm, causing a missed trade, the liability exposure is massive. Legal teams need to be embedded in the IT procurement process now, not after the breach.
Strategic Imperatives for the CFO
The era of cheap, open data is ending. The friction we see today—being blocked from viewing a simple market update video—is the precursor to a tiered internet where access is purchased via reputation and infrastructure investment. CFOs must stop viewing network security as a cost center and start viewing it as a revenue enabler.
Immediate action items include diversifying data ingress points and establishing direct peering relationships with major content hosts where possible. The firms that adapt will see their information edge widen. Those that don’t will find themselves staring at error screens even as their competitors execute.
The market does not forgive latency. As we move deeper into 2026, the ability to bypass the “unusual traffic” filters through legitimate, high-trust B2B partnerships will define the winners. The directory of the future isn’t just about finding vendors; it’s about finding partners who hold the keys to the gate. Ensure your firm is on the whitelist.
