5 Bizarre 3D Printing Projects Worth Trying | BGR
Beyond the Hype: Engineering Utility in Consumer 3D Fabrication
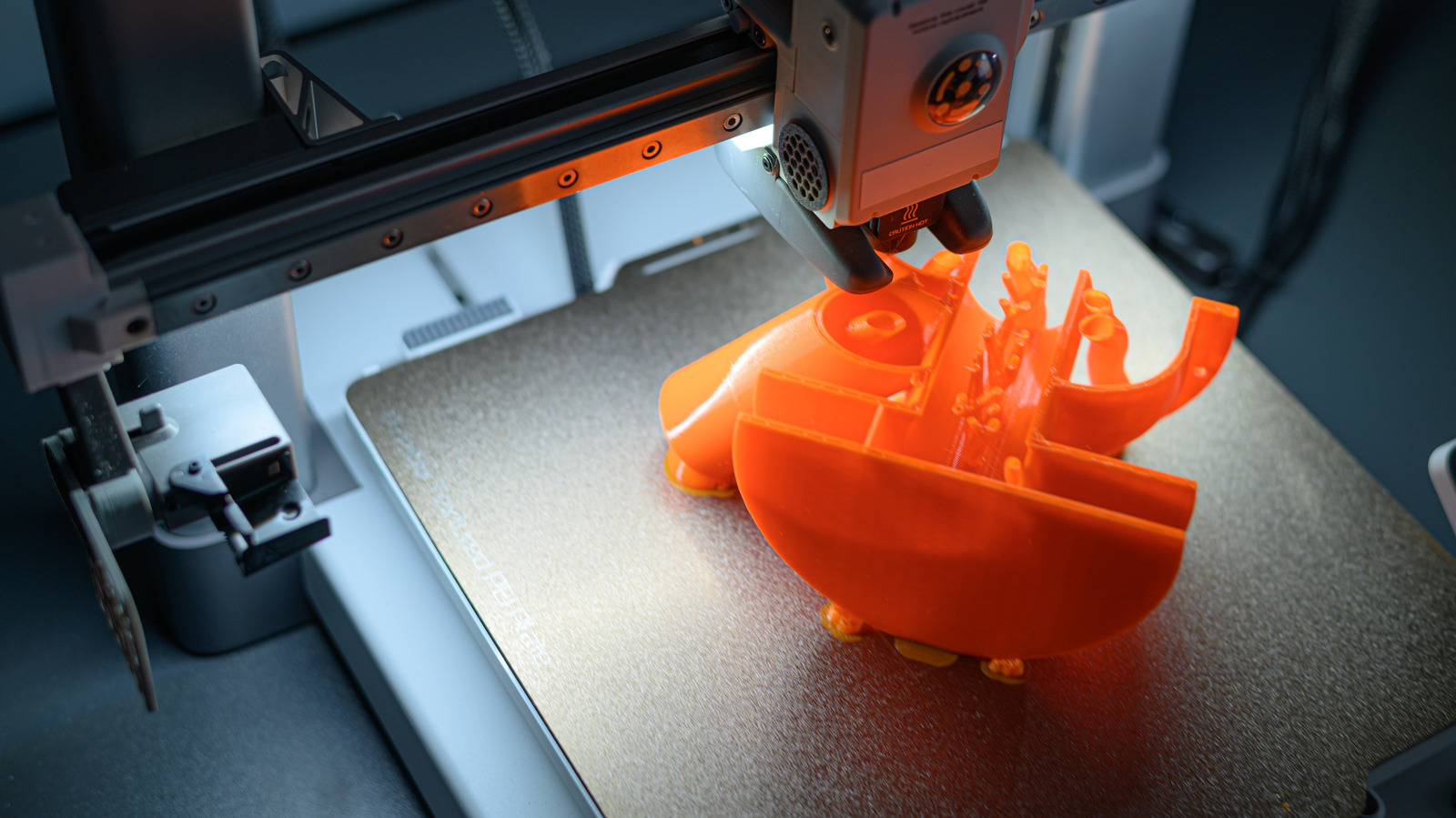
The maker movement often drowns in novelty, churning out Benchys and figurines that serve no purpose other than to clog landfills. However, a subset of distributed manufacturing projects is shifting focus toward functional utility, bridging the gap between hobbyist tinkering and rapid prototyping. While the latest batch of viral 3D printing designs—from keyboard macros to IoT mounts—offers tangible workflow improvements, they introduce subtle hardware security vectors that enterprise IT departments cannot ignore. As we move into Q2 2026, the line between a plastic gadget and a networked endpoint is thinner than ever.
The Tech TL;DR:
- Functional prints like keyboard pressers reduce ergonomic strain but bypass software-based bot detection mechanisms.
- IoT-integrated mounts (wireless chargers) require network segmentation to prevent lateral movement from insecure peripherals.
- Enterprise prototyping must engage cybersecurity audit services before scaling desktop fabrication to production lines.
Examining the recent surge in high-utility print designs reveals a trend toward mechanical automation over digital solutions. Take the keyboard key presser, a mechanical lever designed to hold down specific inputs. While useful for afk grinding in legacy titles like The Elder Scrolls IV, this hardware-level input simulation circumvents software anti-cheat detectors that monitor keystroke timing variance. From an engineering standpoint, the design relies on standard PLA or PETG filaments with a tolerance stack-up of approximately +/- 0.2mm. For a development team testing input latency, this physical workaround is cleaner than running background scripts that trigger heuristic alarms.
Storage solutions also see iteration. The modified coffee bag clip integrates a screw-top spout, replacing single-use plastic ties. This design utilizes a snap-fit assembly requiring no adhesives, reducing volatile organic compound (VOC) exposure during post-processing. While seemingly trivial, the shift toward reusable, printed containment systems aligns with sustainability mandates in corporate procurement. However, when these designs migrate from personal desks to breakroom infrastructure, they fall under physical security policies. Organizations scaling internal fabrication labs should consult cybersecurity risk assessment and management services to ensure proprietary design files do not leak via unsecured printer queues.
IoT Integration and Peripheral Security
The “Cozy Fireplace” wireless charger mount represents a more significant security boundary crossing. By embedding a commercial 5W charging pad into a printed chassis, users create a custom IoT peripheral. Most budget charging pads lack firmware signing or secure boot mechanisms. Connecting such devices to corporate VLANs invites potential attack vectors where power delivery protocols could be exploited for data exfiltration or device fingerprinting. Security architects recommend treating any USB-powered device as untrusted until validated.

Similarly, the “Mobile Exo-Suit” phone stand employs a gear-driven locking mechanism. While mechanically sound, the design assumes the mobile device itself is secure. In a zero-trust architecture, the physical mount is irrelevant if the device management (MDM) profile is compromised. For organizations allowing bring-your-own-device (BYOD) policies, the physical security of the endpoint matters less than the identity verification stack. What we have is where cybersecurity consulting firms provide critical value, auditing not just the network, but the physical hardware supply chain entering the workspace.
Collapsible structures, like the picnic basket design, demonstrate advanced print-in-place mechanics. These require precise temperature control and cooling fan management to prevent layer adhesion failure during the folding hinge creation. Failure here isn’t just aesthetic; it indicates a calibration drift in the printer’s motion system that could affect functional parts later.
Implementation: Securing the Fabrication Pipeline
Deploying these designs in a professional environment requires validating the G-code itself. Malicious inserts can damage printer hardware or alter dimensional accuracy. Below is a curl command example to verify the status of a networked printer API before sending a job, ensuring the device is not in a compromised state.
curl -X GET http://192.168.1.50/api/v1/status -H "Authorization: Bearer $PRINTER_TOKEN" -H "Content-Type: application/json" | jq '.security.firmware_signed'Returning true confirms the firmware integrity check passed. If the response is null or false, the job should be quarantined. This level of scrutiny mirrors the diligence required by roles such as the Associate Director of Research Security found in academic and corporate institutions, where protecting intellectual property during the prototyping phase is paramount.
Material and Security Specification Matrix
| Project Component | Recommended Material | Security Risk Level | Deployment Context |
|---|---|---|---|
| Keyboard Presser | PETG (High Durability) | Low (Physical Only) | QA Testing / Legacy Support |
| Wireless Charger Mount | PLA (Low Thermal Conductivity) | High (IoT/Power) | Secure VLAN Required |
| Collapsible Basket | TPU (Flexible Hinge) | None | Logistics / Storage |
| Exo-Suit Stand | ABS (Heat Resistance) | Low | Desktop Peripheral |
The integration of additive manufacturing into daily workflows is inevitable, but it demands a shift in security posture. As Microsoft AI and other tech giants expand their security directorates, the focus is increasingly on the edge devices connecting to their clouds. A 3D printer is no longer just a tool; it is a networked computer capable of executing physical actions. Organizations must treat their fabrication labs with the same rigor as their server rooms.
“The convergence of physical prototyping and digital security means every printed part is a potential endpoint. We need Research Security Managers to oversee the integrity of the design-to-production pipeline.”
these bizarre projects prove that 3D printing has matured past novelty. They solve specific latency and ergonomic bottlenecks without requiring software overhead. However, scaling this utility requires professional oversight. Whether you are securing a wireless charger or auditing a print farm, engaging specialized cybersecurity audit services ensures that your innovation does not develop into your vulnerability.
Disclaimer: The technical analyses and security protocols detailed in this article are for informational purposes only. Always consult with certified IT and cybersecurity professionals before altering enterprise networks or handling sensitive data.
